Ukraine Police Arrest Cybercriminals Behind Clop Ransomware Attacks
Ukrainian law enforcement officials reported the arrest of the Clop ransomware group on Wednesday. The organization had been disrupting infrastructure and carrying attacks around the world since at least 2019, according to The Hacker News.
Six defendants were charged as part of an international operation involving Ukraine’s National Police and authorities from Interpol, Korea, and the United States for running a double extortion scheme that threatened victims who refused to pay a ransom with the leak of sensitive financial, customer, or personal data. According to National Police, the ransomware attacks caused a whopping $500 million in damage.
Ukrainian police stated, “law enforcement has managed to shut down the infrastructure from which the virus spreads and block channels for legalizing criminally acquired cryptocurrencies”.
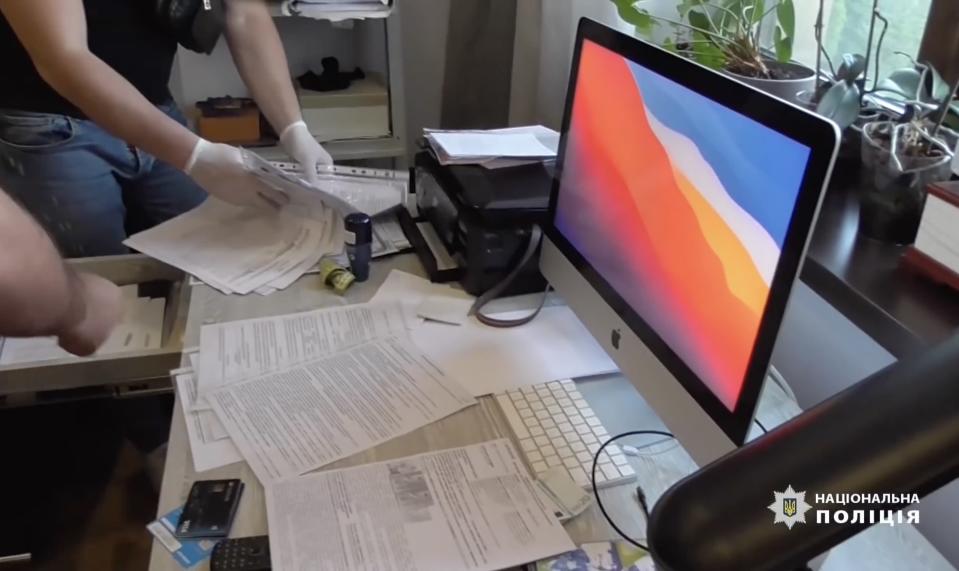
Police officers allegedly conducted 21 searches in the Ukrainian capital Kyiv, including the defendants’ homes, leading to the seizure of computer equipment, luxury cars, and cash worth 5 million hryvnias ($184,679).
Cybercriminals could face up to eight years in prison
On charges of illegally interfering with the operation of computers, automated systems, computer networks, or telecommunications networks, the alleged perpetrators face up to 8 years in prison. However, it is unclear whether those arrested are employees or key developers of the ransomware operation.
As of 1 pm Eastern Time, CL0P-LEAKS, the dark web portal used by Clop to distribute stolen material, is still up and running. It means that the entire infrastructure may not have been shut down.
Since 2019, the threat actor has been linked to several high-profile attacks, including attacks on E-Land, Accellion, Qualys, Software AG IT, ExecuPharm, Indiabulls, and several universities, counting Maastricht University, Stanford University Medical School, the University of Maryland and the University of California.
Clop’s arrests are the latest in a series of operations conducted by government agencies in recent months to combat illicit activity in cyberspace, such as TrickBot, Emotet, ANoM, and Slilpp. Earlier last month, a joint investigation by French and Ukrainian officials broke up the cartel linked to the Egregor ransomware.