Ongoing attacks are targeting unsecured mission-critical SAP apps

Threat actors are targeting mission-critical SAP applications unsecured against already patched vulnerabilities, exposing the networks of commercial and government organizations to attacks.
Over 400,000 orgs worldwide and 92% of Forbes Global 2000 use SAP’s enterprise apps for supply chain management (SCM), enterprise resource planning (ERP), product lifecycle management (PLM), and customer relationship management (CRM).
SAP and cloud security firm Onapsis warned of these ongoing attacks today, and have worked in partnership with the Cybersecurity and Infrastructure Security Agency (CISA) and Germany’s cybersecurity agency BSI to warn SAP customers to deploy patches and survey their environments for unsecured apps.
“We’re releasing the research Onapsis has shared with SAP as part of our commitment to help our customers ensure their mission-critical applications are protected,” Tim McKnight, SAP Chief Security Officer, said.
“This includes applying available patches, thoroughly reviewing the security configuration of their SAP environments, and proactively assessing them for signs of compromise.”
Targeted SAP vulnerabilities
The threat intelligence collected and published by Onapsis in coordination with SAP shows that they “are not aware of known customer breaches” resulting from this malicious activity.
However, it reveals that SAP customers still have unsecured applications in their environments visible via the Internet, and exposing the organizations to infiltration attempts via attack vectors that should’ve been patched years ago.
Since mid-2020, when Onapsis started recording exploitation attempts targeting unpatched SAP apps, the firm’s researchers found “300 successful exploitations through 1,500 attack attempts from nearly 20 countries between June 2020 and March 2021.”
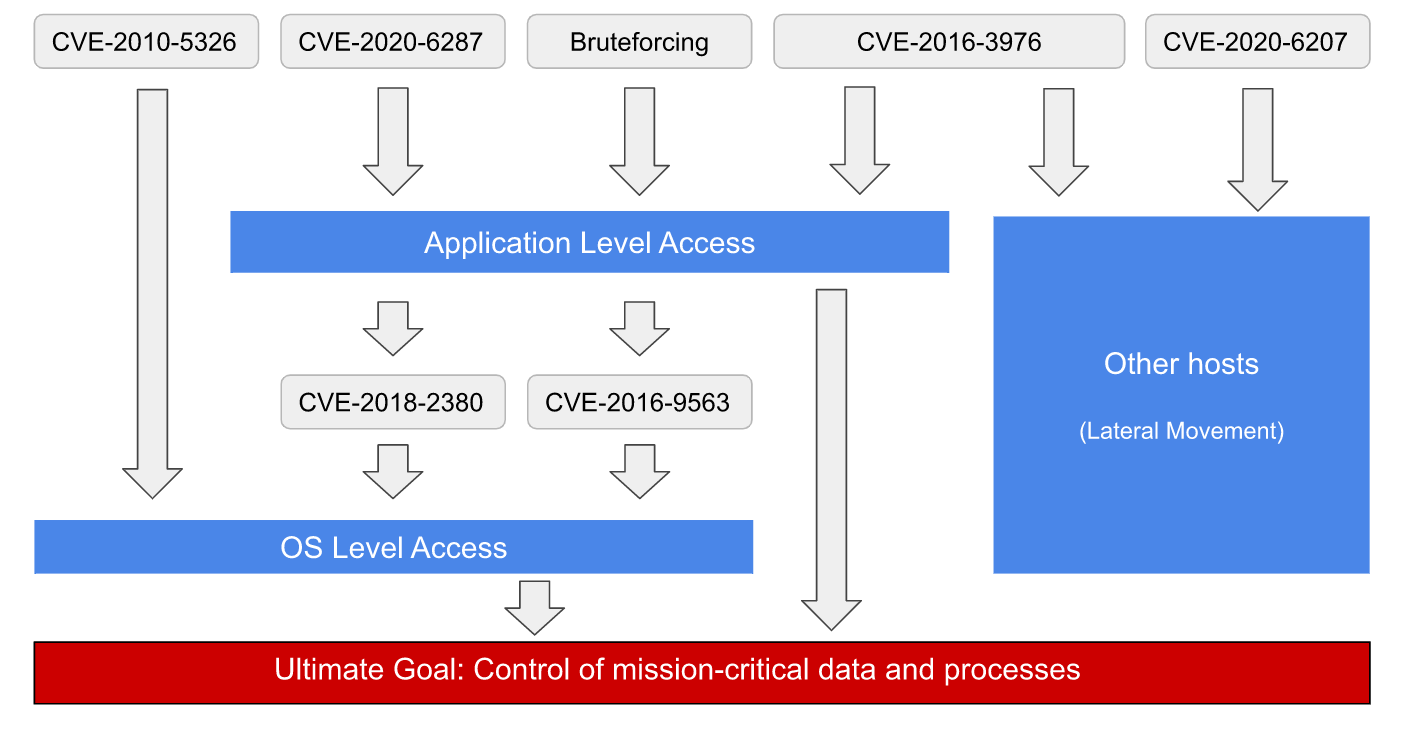
The threat actors behind these attacks have exploited multiple security vulnerabilities and insecure configurations in SAP applications in attempts to breach the targets’ systems.
In addition, some of them have also been observed while chaining several vulnerabilities in their attacks to “maximize impact and potential damage.”
“Observed exploitation techniques would lead to full control of the unsecured SAP applications, bypassing common security and compliance controls, and enabling attackers to steal sensitive data, perform financial fraud or disrupt mission-critical business processes by deploying ransomware or stopping operations,” Onapsis explained.
“With remote access to SAP systems and mission-critical applications, the need for lateral movement is nearly eliminated, enabling attackers to reach and exfiltrate business-critical data more quickly.”
The vulnerabilities and attack methods used throughout this ongoing malicious activity highlight in the joint threat report published by Onapsis are:
- Brute-force attacks targeting unsecured high-privilege SAP user account settings
- CVE-2020-6287 (aka RECON): a remotely exploitable pre-auth vulnerability that enables unauthenticated attackers to take over vulnerable SAP systems.
- CVE-2020-6207: maximum severity pre-auth vulnerability that could also lead to the takeover of unpatched SAP systems (fully-working exploit was released in January 2021, on GitHub). Onapsis has seen a significant increase in exploit activity targeting this bug since the exploit was published, detecting 756 probes from 34 distinct IP addresses.
- CVE-2018-2380: enables threat actors to escalate privileges and execute OS commands after exploitation, allowing them to gain access to the database and to move laterally across the network (34 incoming exploitation attempts from 10 distinct IPs were detected by Onapsis, with web shells being deployed after successful exploitation)
- CVE-2016-95: attackers can exploit this bug to trigger denial-of-service (DoS) states and gain unauthorized access to sensitive information.
- CVE-2016-3976: remote attackers can exploit it to escalate privileges and to read arbitrary files via directory traversal sequences, leading to unauthorized disclosure of information. Exploits that can be used to fully compromise unpatched and exposed SAP systems were publicly released in 2016.
- CVE-2010-5326: allows unauthenticated threat actors to execute OS commands and access the SAP app and the connected database, thus gaining complete and unaudited control of the SAP business information and processes. (206 exploitation attempts detected since mid-2020, coming from 10 unique IP addresses)
According to an alert issued by CISA today, organizations impacted by these attacks could experience:
- theft of sensitive data,
- financial fraud,
- disruption of mission-critical business processes,
- ransomware, and
- halt of all operations.
Patching vulnerable SAP systems should be a priority for all defenders since Onapsis also found that attackers start targeting critical SAP vulnerabilities within less than 72 hours, with exposed and unpatched SAP apps getting compromised in less than three hours.
Are your SAP applications secure? Read @Onapsis’ latest Alert to learn how your organization can protect itself from recent threat actor activity by applying necessary updates and mitigations. https://t.co/YTsliuRpMW #Cybersecurity #InfoSec
— US-CERT (@USCERT_gov) April 6, 2021
Threat mitigation measures
The vulnerabilities abused in these ongoing attacks only impact customer deployments, including those in their own data centers, managed colocation environments, or customer-maintained cloud infrastructures.
SAP-maintained cloud solutions are not affected by these vulnerabilities, according to the threat report.
SAP customers are advised to take action to mitigate the risk posed by this active threat targeting their SAP products’ vulnerabilities and insecure configurations by:
- Immediately perform a compromise assessment on SAP applications that are still exposed to the vulnerabilities mentioned herein, or that have not been promptly secured upon the release of the relevant SAP security patches. Internet-facing SAP applications should be prioritized.
- Immediately assess all applications in the SAP environment for risk, and immediately apply the relevant SAP security patches and secure configurations.
- Immediately assess SAP applications for the existence of misconfigured and/or unauthorized high-privilege users and perform a compromise assessment on at-risk applications
- If assessed SAP applications are currently exposed and mitigations cannot be applied in a timely manner, compensating controls should be deployed and activity monitored to detect any potential threat activity until such mitigations are implemented.
“The critical findings noted in our report describe attacks on vulnerabilities with patches and secure configuration guidelines available for months and even years,” Onapsis CEO Mariano Nunez added.
“Unfortunately, too many organizations still operate with a major governance gap in terms of the cybersecurity and compliance of their mission-critical applications, allowing external and internal threat actors to access, exfiltrate and gain full control of their most sensitive and regulated information and processes.
“Companies that have not prioritized rapid mitigation for these known risks should consider their systems compromised and take immediate and appropriate action.”





![AirTag hacked for the first time by security researcher [Video]](https://pr24.news/wp-content/uploads/2021/05/The-Rewind-iPhone-12-Purple-Edition-Find-My-AirTag-768x402.jpg)