GitHub Infrastructure Used to Mine Cryptocurrency
Software developers have reported a series of malicious activities on their repositories, having the end purpose of mining cryptocurrency. The attacks have been happening since November 2020, the first report being made by a French software engineer.
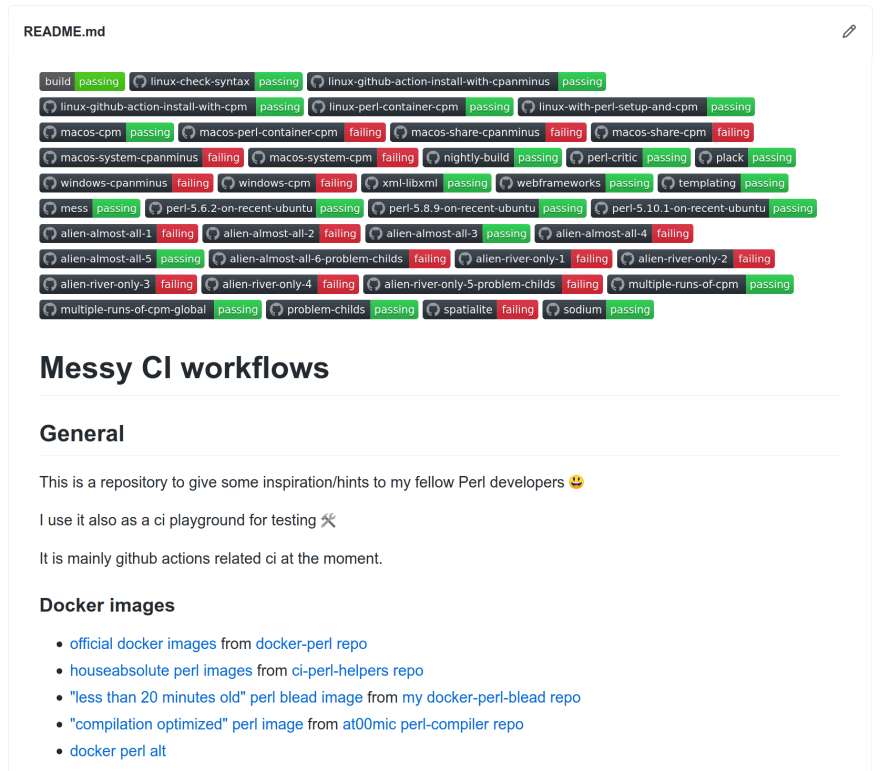
It looks like the threat actors are abusing the GitHub Actions feature that was implemented with the purpose of allowing automatic execution of software workflows.
The threat actors seem to be targeting repositories that have this specific feature enabled in order to be able to add malicious GitHub Actions and fill Pull Requests that will later help them execute malicious attacker code.
In a phone call today, Dutch security engineer Justin Perdok told The Record that at least one threat actor is targeting GitHub repositories where Actions might be enabled. The attack involves forking a legitimate repository, adding malicious GitHub Actions to the original code, and then filing a Pull Request with the original repository in order to merge the code back into the original.
But the attack doesn’t rely on the original project owner approving the malicious Pull Request. Just filing the Pull Request is enough for the attack, Perdok said.
Interestingly enough is the fact that in the most recent attacks, threat actors are executing their own malicious code for mining cryptocurrency from the miners existing on the infrastructure of the code repository hosting service, and in some cases, the attackers could deploy hundreds of miners within a single attack.
One of my repo’s just got hit with a similar attack. Account in question has a bunch of other open PR’s that currently have miners running. https://t.co/PZxApykuO9 pic.twitter.com/zugl7mFK0K
— Justin Perdok (@JustinPerdok) April 2, 2021
This type of attack has a significant impact on the computational capabilities of the abused infrastructure, using GitHub Actions to facilitate CI/CD automation and also scheduling tasks.
It’s quite concerning that this particular attack abuses GitHub’s own infrastructure in order to spread malware and mine cryptocurrency on their servers by first forking a legitimate repository that has GitHub Actions enabled, then the malicious code is being injected into the forked version, filling a Pull Request for the original repository maintainers in order to merge the code back.






