NSA Issues Guidance on Zero Trust Implementation
Critical Infrastructure Security
,
Digital Identity
,
Endpoint Security
Critical Networks Within National Security Systems Should Implement Zero Trust

The US National Security Agency has issued its zero trust guidance aimed at securing critical networks and sensitive data within key federal agencies. The NSA adds it is also assisting Defense Department the zero trust implementations.
See Also: Live Webinar | SolarWinds Breach: If Cyber Companies Can Get Hit, Do You Stand A Chance?
New guidance issued on Thursday describes some of the basic zero trust principles such as ‘assume breach,’ and lays down zero trust design concepts. The agency also describes threat scenarios and how organizations can prevent these attacks using the new zero-trust models.
“NSA strongly recommends that a Zero Trust security model be considered for all critical networks within National Security Systems, the Department of Defense’s critical networks, and Defense Industrial Base critical networks and systems,” says the guidance. “Adopting Zero Trust will enable systems administrators to control how users, processes, and devices engage with data. These principles can prevent the abuse of compromised user credentials, remote exploitation, or insider threats, and even mitigate effects of supply chain malicious activity.”
The agency also adds it is assisting Defense Department customers in piloting zero trust systems and is set to release additional guidance on further zero trust implementation.
Zero Trust Design Concept
The NSA describes four key elements that organizations should consider before implementing zero trust models. These are:
- Defining mission outcomes: Organizations should adopt zero trust models after determining organization-specific requirements which should be based on their critical data, assets, applications and services or DAAS.
- Architect from the inside out: The focus of any organizations should be to protect critical DASS first and then securing all paths to access them.
- Define access: Organizations should define access to DAAS and create access control policies and apply them consistently across all environments such as LAN, WAN, endpoint, perimeter, mobile, among others.
- Inspect and log all traffic before acting: Ensure there is full visibility to all activity across all layers from endpoints and the network to enable analytics that can detect suspicious activity.
Attack Scenarios
The agency describes three attacks scenarios and how zero trust models can help prevent these attacks.
- Compromised user credentials: When a threat actor uses compromised credentials, they mostly use an unauthorized device, either through remote access or with a rogue device joining the organization’s wireless LAN. By deploying zero trust, NSA says organizations prevent unauthorized checks, access is denied and any malicious activity is logged.
- Remote exploitation or insider threat: In a non-zero trust environment, threat actors use the user’s credentials, enumerate the network, escalate privileges, and move laterally to compromise vast stores of data. However, with zero trust, the compromised user’s credentials and the device are already assumed to be malicious, and the network is segmented, limiting both enumeration and lateral movement opportunities.
- Compromised supply chain: With zero trust, embedding of malicious codes into popular enterprise network devices or applications can be avoided, as such malicious applications will not be inherently trusted. Through a mature implementation of zero trust, data would be tightly controlled, minimized, monitored and segmented.
Need for Zero Trust
Kevin Dunn, president at security firm Greenlight, says government agencies such as NSA need to set tight security standards, as they are the most frequent targets of cyber threat actors. However, he notes that the private sector is equally vulnerable to similar threats.
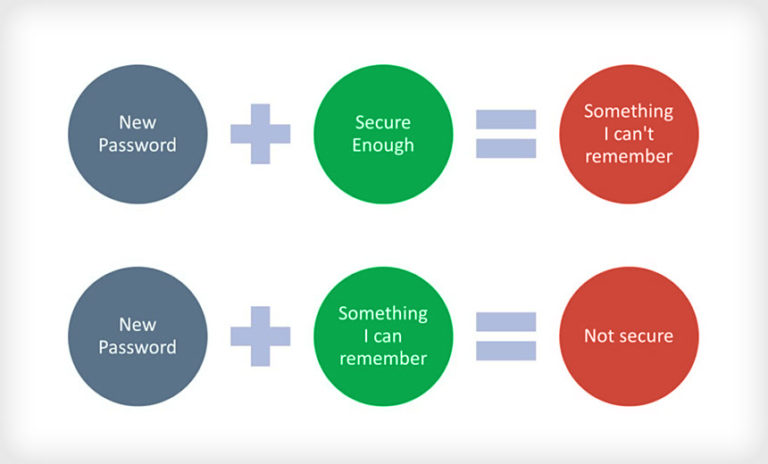
“Any organization that is uncertain about the value of zero trust should start with an audit of their identities, networks, devices and applications – undoubtedly, they will find cases of shadow IT, zombie accounts, and over-privileged users that represent clear and present danger,” Dunn says. “Implementing a zero trust model across identities, networks, devices and applications can be the difference between a limited hack with insignificant damage or a major incident with loss of critical data.”
“The principles of zero trust outlined by the NSA are a natural progression from CISA’s Continuous Diagnostics and Mitigation (CDM) program developed in 2012,” Oliver Tavakoli, CTO at security firm Vectra adds. “Private entities are already ahead of the federal government in adopting these Zero Trust principles, though that journey is by no means complete.”
Joseph Carson, advisory CISO at Thycotic notes that one significant drawback with zero trust is its limitation to focus on the business value. “The term zero trust resonates best within the security and risk teams, however, with the business it is just another security control,” Carson says. “Moving forward, the top focus of security must be on how it adds business value followed by how it reduces business risks and increases business resilience. Unfortunately, for now, we continue to focus on the threats.”