Microsoft Issues PrintNightmare Security Update
Governance & Risk Management
,
IT Risk Management
,
Patch Management
Company Also Updates Risk Mitigation Advice
This story has been updated.
See Also: Live Panel | Zero Trusts Given- Harnessing the Value of the Strategy
The Cybersecurity and Infrastructure Security Agency reported Tuesday that Microsoft has released an emergency out-of-band security update to address the PrintNightmare (CVE-2021-34527) Windows Print spooler service flaw.
Microsoft warns that it’s aware of active exploits in the wild and says: “We recommend that you install these updates immediately,” adding that organizations unable to install these updates should apply workaround advice issued earlier.
Microsoft updated its mitigation advice for the “PrintNightmare” remote code execution vulnerability affecting Windows Print Spooler on Saturday. This was primarily an interim measure ahead of issuing the emergency updates, but still applies to those unable to implement the latest updates.
The Windows Print Spooler vulnerability has been assigned CVE-2021-34527 by Microsoft. It has been given a Common Vulnerability Scoring System base rating of 8.8, which is close to a critical score of 9.
Exploiting this remote code execution vulnerability in the Windows Print Spooler service enables attackers to perform unauthorized privileged file operations, says Microsoft. The company describes how an attacker could use the vulnerability exploit to run arbitrary code with system privileges; install programs; view, change, or delete data; or create new accounts with full user rights.
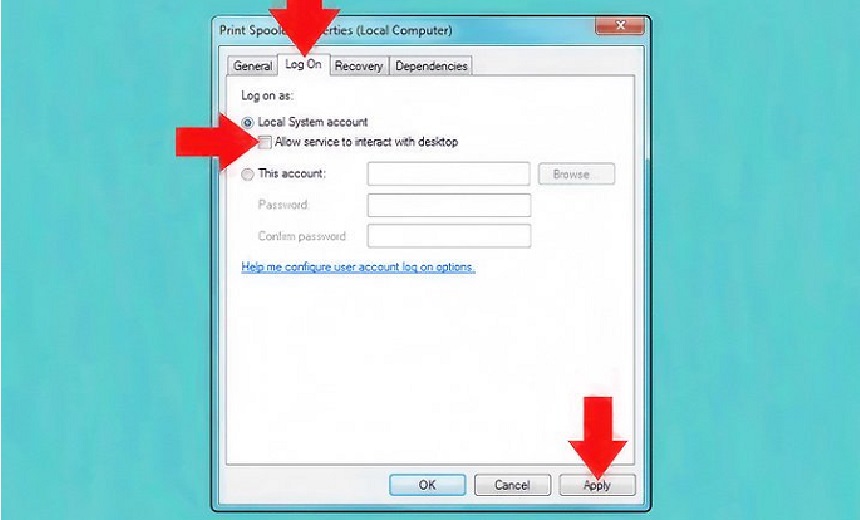
For organizations unable to implement the security updates, Microsoft advises disabling the Windows Print Spooler service at least for inbound remote printing through Group Policy. “Group policy will block the remote attack vector by preventing inbound remote printing operations. The system will no longer function as a print server, but local printing to a directly attached device will still be possible,” Microsoft notes.
Users should also apply the patch released on June 8, 2021, for an earlier flaw assigned CVE-2021-1675 which addresses a different vulnerability in RpcAddPrinterDriverEx() using a different attack vector. The RpcAddPrinterDriverEx() function is used to install a printer driver on a system.
Microsoft now also says that membership and nested group membership of some entities needs to be checked, with the number of members kept as low as possible, ideally zero. It notes, however, that removing members from some of these groups may lead to compatibility issues. The groups are:
- Administrators;
- Pre-Windows 2000 Compatible Access;
- Network Configuration Operators Group Object;
- Cryptographic Operators Group Object;
- Local account and member of administrators group;
- Domain Controllers;
- Read-Only Domain Controllers;
- Enterprise Read-Only Domain Controllers;
- Certificate Admins;
- Schema Admins;
- Enterprise Admins;
- Group Policy Admins;
- Power Users;
- System Operators;
- Print Operators;
- Backup Operators;
- RAS, or Remote Access Servers;
Microsoft also recommends organizations use tooling such as Microsoft Defender 365 to monitor potentially malicious activity.
CISA Advice Covers First Steps
Prior to the emergency updates being issued, the Cybersecurity and Infrastructure Security Agency also issued a warning urging administrators to disable the Windows Print Spooler service in Domain Controllers and systems that do not print.
“Additionally, administrators should employ the following best practice from Microsoft’s how-to guides, published Jan. 11, 2021: “Due to the possibility for exposure, domain controllers and Active Directory admin systems need to have the Print spooler service disabled. The recommended way to do this is using a Group Policy Object,” CISA notes.