A Call for Cryptocurrency Regulation
Business Continuity Management / Disaster Recovery
,
Fraud Management & Cybercrime
,
Fraud Risk Management
Coalition Offers a Framework for Disrupting Attacks

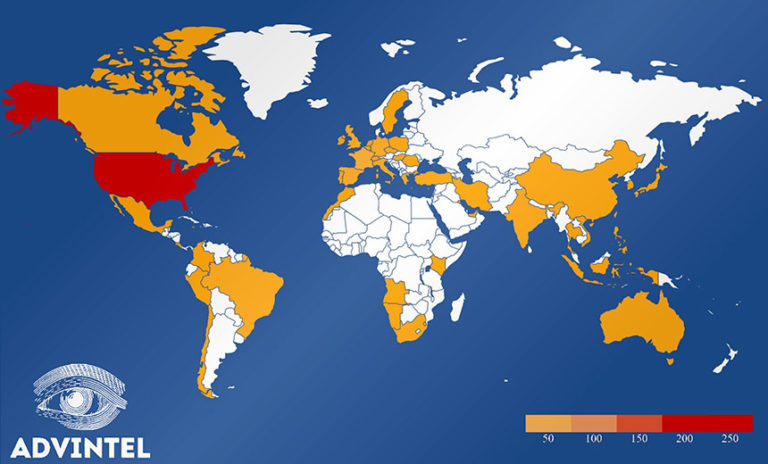
A coalition of government agencies and security firms has released a framework for how to disrupt ransomware attacks that calls for expanded regulation of the global cryptocurrency market to better track the virtual coins paid to cybercriminals during extortion schemes.
See Also: The Cost of OT Cybersecurity Incidents and How to Reduce Risk
On Thursday, the Institute for Security and Technology’s Ransomware Task Force published the framework, which features 48 proposals. It calls for a coordinated, international diplomatic and law enforcement effort to combat these cyberthreats – for example, by discouraging nation-states from harboring cybercriminals and their operations.
The group also encourages the White House to take the lead on addressing ransomware by creating a group that includes representatives of the National Security Council, the office of the National Cyber Director, and security companies to coordinate the effort.
The Ransomware Task Force also recommends that the U.S. and other nations create a response and recovery fund to support the responses to ransomware. The framework also calls for laws that would require organizations to report ransomware payments.
Tackling Ransomware
“One thing is clear – ransomware is a threat to our national security,” says Secretary of Homeland Security Alejandro Mayorkas, who has made ransomware one of the top cybersecurity priorities for his department. “Like most cyberattacks, ransomware exploits the weakest link. In recent months, ransomware attacks in hospitals in New York, Nebraska, Oregon and in Michigan have taken place during what is an unprecedented pandemic.”
Although the framework offers dozens of suggestions, it emphasizes better tracking and regulating the markets for bitcoin and other cryptocurrencies – the favorite form of payment for cybercriminal organizations and their affiliates.
“The use of cryptocurrency adds to the challenge of identifying ransomware criminals, as payments with these currencies are difficult to attribute to any individual,” according to the report. “Often the money does not flow straight from ransomware victim to criminal; it travels through a multi-step process involving different financial entities, many of which are novel and are not yet part of standardized, regulated financial payments markets.”
National Security Threat
Philip Reiner, CEO of the Institute for Security and Technology, notes that the goal of the framework is to emphasize that ransomware has grown into a problem that goes far beyond cybercriminals extorting companies.
“Ransomware has risen to the level of being a much broader societal challenge, and a national security threat – not just the niche computer crime that impacts organizations,” Reiner says. “We were really struck by the notion that with all of the resources that governments and companies around the world have to bring to bear on a problem like this …. How is it that this wreck is continuing to metastasize, and why hasn’t someone been able to put together all of the right people to better direct resources?”
Big Payoffs
In March, Chainalysis published a report that estimated criminal groups reaped $370 million in ransom payments in 2020, up 336% from 2019.
A report published this week by incident response firm Coveware found that in the first quarter of this year, the average cyber extortion payoff reached $220,298, a 43% increase from the previous quarter. This increase is being driven, in part, by ransomware gangs taking advantage of unpatched vulnerabilities in the older versions of the Accellion File Transfer Appliance (see: Cyber Extortion Thriving Thanks to Accellion FTA Hits).
In the report, the Ransomware Task Force notes that in 2020, about 2,400 U.S. organizations were targeted in ransomware attacks, including 1,700 schools, colleges and universities as well as 560 healthcare organizations (see: Ransomware Attacks in Healthcare Surging).
Disrupting the Ransomware Business Model
The new framework emphasizes that disrupting the ransomware business model – including the ability for cybercriminals to extort cryptocurrency payments from victims and then hide those transactions from law enforcement agencies – is key to reducing these types of attacks.
An important step, the framework notes, is the adoption of laws and regulations designed to better track the virtual currency that flows from cryptocurrency exchanges, crypto kiosks and over-the-counter trading desks where cybercriminals can hide the transactions and cash out their earnings thanks to loose rules that are now in place.
Agencies such as the U.S. Treasury Department and the Securities and Exchange Commission, along with their international counterparts, also need to improve enforcement of existing rules and regulations, such as anti-money laundering laws and laws that combat financing of terrorism.
Some laws, such as the Cybersecurity Information Sharing Act of 2015, need updates, the framework points out.
Additional Steps
The framework also notes that financial institutions need to address ransomware attacks.
Banks should “pursue SEC enforcement of cryptocurrency businesses that fail to register as broker-dealers, transfer agents, clearing agencies, and money service businesses, with particular focus on mixing services that obfuscate criminal transactions with legal traffic,” the framework states.
Other recommendations in the task force report include:
- Encouraging cryptocurrency exchanges, trading desks and others to share information with law enforcement agencies about suspicious transactions;
- Providing law enforcement agencies with the ability to issue letters to crypto entities requesting that ransomware funds be frozen as proceeds of crime that can then be seized by the government;
- Creating the ability to blacklist digital wallets associated with criminal gangs;
- Improving civil recovery and asset forfeiture processes;
- Building an insurance-sector consortium to share ransomware loss data.
Targeting Infrastructure
The task force also says much more needs to be done to disrupt the infrastructure that cybercriminals use to support their malicious activities.
It calls on Congress to update the Computer Fraud and Abuse Act so that infrastructure providers will be encouraged to report criminal activity.
“If a hosting company is made aware that a customer is conducting attacks from one of the hosting company’s servers, they can typically shut down the customer’s service due to a violation of the company’s terms of service,” the report notes. “In a less clear scenario, if a telecommunications company is provided a signature that identifies malicious network traffic and they block the traffic from transiting their network, thereby disrupting the malicious activity, the company may have some legal liability.”
Other Efforts
Earlier this month, the U.S. Department of Justice started its own Ransomware and Digital Extortion Task Force to target the “ransomware criminal ecosystem” (see: DOJ Launches Task Force to Battle Ransomware Threat).
DHS Secretary Mayorkas also announced in March that the agency would conduct a 60-day “sprint” exercise focused on battling ransomware.