Zyxel Warns of Attacks on Its Firewall, VPN Products
Endpoint Security
,
Governance & Risk Management
,
IT Risk Management
Company Advises Users to Maintain Proper Security Policies as It Prepares Hotfix
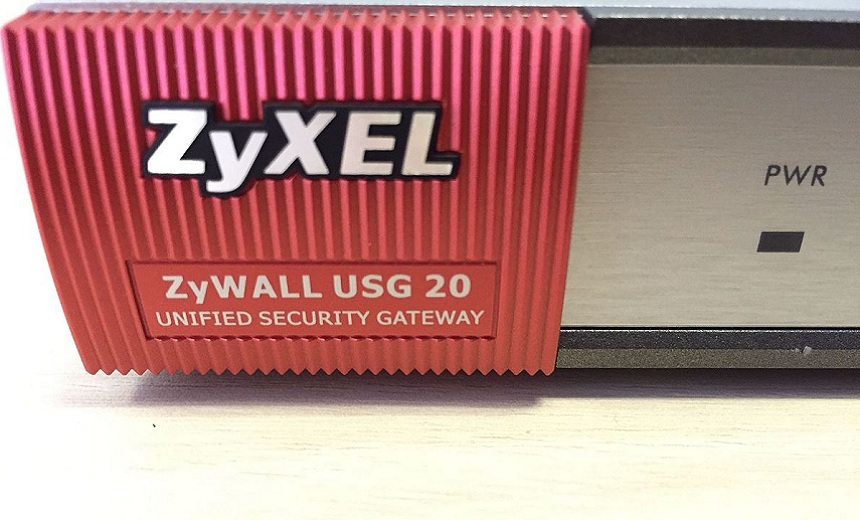
Zyxel, a Taiwanese networking device manufacturer, is notifying customers about an ongoing series of attacks on some of its enterprise firewall and VPN products and is advising users to maintain proper remote access security policies as it prepares a hotfix.
See Also: Live Panel | Zero Trusts Given- Harnessing the Value of the Strategy
The company says that attackers are targeting its enterprise firewall and VPN server solutions in the USG, ATP, USG FLEX, ZyWALL and VPN series that have remote management or SSL VPN enabled.
“The threat actor attempts to access a device through WAN; if successful, they then bypass authentication and establish SSL VPN tunnels with unknown user accounts, such as ‘zyxel_sllvpn’, ‘zyxel_ts’, or ‘zyxel_vpn_test’, to manipulate the device’s configuration,” the company says in a statement.
The attackers are using hard-coded accounts to access a device through WANs, Zyxel reports.
Vulnerability Disclosure
Following the disclosure of the vulnerability, Zyxel says it determined that maintaining best practices for remote access security policies could help prevent attacks.
The company has released a standard operating procedure to guide users through setting up a remote access policy and is also working on a hotfix with further countermeasures to mitigate the threat.
“Zyxel already offers a mitigation firmware update that will actively guide users to follow general security best practices to reduce the attack surface,” the company notes.
A Twitter post by JAMESWT, who describes himself as an independent malware hunter, contained a letter that looked like a statement from Zyxel to its customers. The letter recommended disabling HTTP and HTTPS services from the WAN. If WAN is used, users must restrict untrusted sources (e.g., internet address) and enable GeoIP filtering, it says.
#Zyxel
We recently became aware of a sophisticated threat actor targeting a small subset of Zyxel security appliances that have remote management or SSL VPN enabled, namely in the USG/ZyWALL, USG FLEX, ATP, and VPN series running on-premise ZLD firmware. https://t.co/m76suB3VoG pic.twitter.com/EpBsc715kI— JAMESWT (@JAMESWT_MHT) June 24, 2021
Step-by-Step Mitigation
Zyxel, in a blog post, explains step-by-step mitigation and best practices for its customers.
For example, Zyxel advises companies that allow employees to access an office network via SSL VPN for remote working to “configure the perimeter firewall correctly based on least privilege principle. For example, if remote admin access/SSLVPN is required, then we can implement a list of restricted geo-IP while explicitly allowing access from a set of source IP or country.”
“Many victims could have prevented a data breach if they’d only updated their OS and apps,” the company notes, advising timely patching along with other basic steps, such as using multifactor authentication and implementing anti-phishing programs.
Earlier Warnings of Likely Attacks
In January, Dutch security firm Eye Control said that attackers had stepped up scanning for vulnerable Zyxel products, including VPN gateways, access point controllers and firewalls (see: Researchers Warn Attackers Are Scanning for Zyxel Products).
Eye Control researchers identified a firmware vulnerability in about 100,000 Zyxel products, including VPN gateways, access point controllers, and firewalls that could be exploited to install a hard-coded backdoor that could give threat actors remote administrative privileges. (see: 100,000 Zyxel Devices Vulnerable to Backdoor)
Then in April, the Multi-State Information Sharing and Analysis Center, or MS-ISAC, issued an alert stating the Zyxel vulnerability poses a risk for enterprises and government agencies that use the company’s security and networking products.
MS-ISAC noted that a threat actor could use the vulnerability to gain administrative access to the inner parts of a targeted network and further escalate privileges. MS-ISAC echoed Zyxel’s advice on deploying security best practices in addition to deploying appropriate updates provided by Zyxel immediately after appropriate testing.
Other Vulnerable VPNs
Security researchers and government agencies have been warning about vulnerabilities in VPNs and access products. For example, late last year, the U.S. Cybersecurity and Infrastructure Security Agency warned about a password leak that could affect vulnerable Fortinet VPNs, which could lead to further exploitation.
The agency’s alert came after security researchers reported that hackers had claimed to have published the leaked passwords on underground forums. While CISA stopped short of confirming the authenticity of the password leak, the agency urged those using Fortinet equipment to check with the company about patches and to review logs to check for suspicious activity (see: CISA Warns of Password Leak on Vulnerable Fortinet VPNs).