Senate SolarWinds Hearing: 4 Key Issues Raised
Cyberwarfare / Nation-State Attacks
,
Forensics
,
Fraud Management & Cybercrime
Issues Include Attackers’ Use of Amazon’s Infrastructure

The Senate Intelligence Committee’s hearing Tuesday about the supply chain attack that affected SolarWinds and dozens of other companies and federal agencies answered some questions about what went wrong but also raised four key issues:
See Also: Live Webinar | The EVIL-Ution Of Ransomware In 2021-Top Protection Tips
- How Amazon Web Services may have been used to host malicious infrastructure;
- Why the attackers conducted a “dry run”;
- What the true motives were for the attack, which apparently was waged by Russian hackers;
- How the incident could lead to better cyberthreat and intelligence information sharing.
White House Update
Meanwhile, White House press secretary Jen Psaki said Tuesday that the Biden administration was still weighing its options for how to respond to the attack, but the response could come soon.
“We have asked the intelligence community to do further work to sharpen the attribution that the previous administration made about precisely how the hack occurred, what the extent of the damage is and what the scope and scale of the intrusion is. And we’re still in the process of working that through now,” Psaki told reporters. “But it will be weeks, not months before we respond, but I’m not going to get ahead of the conclusion of that process.”
Investigators believe that nine federal agencies, as well as 100 private sector organizations, were compromised as part of the attack, Deputy National Security Adviser Anne Neuberger said earlier this month.
On Wednesday, The Washington Post reported that NASA and the Federal Aviation Administration were among the agencies that were targeted.
The supply chain attack was launched when hackers planted a backdoor known as “Sunburst” within an update for SolarWinds’ Orion network monitoring platform. Then, 18,000 of the company’s customers downloaded the update, and some of those were further targeted for follow-on attacks.
Here’s a closer look at four critical issues raised at Tuesday’s hearing.
1. Did Hackers Leverage Amazon Web Services?
While senators heard from Microsoft, FireEye, CrowdStrike and SolarWinds at the hearing, Amazon executives, who were invited to testify, declined.
When giving his opening remarks, Florida Republican Sen. Marco Rubio, the vice chair of the intelligence committee, noted: “The operation we will be discussing today utilized Amazon’s infrastructure, at least in part, to be successful. I had hoped Amazon would provide their cooperation.”
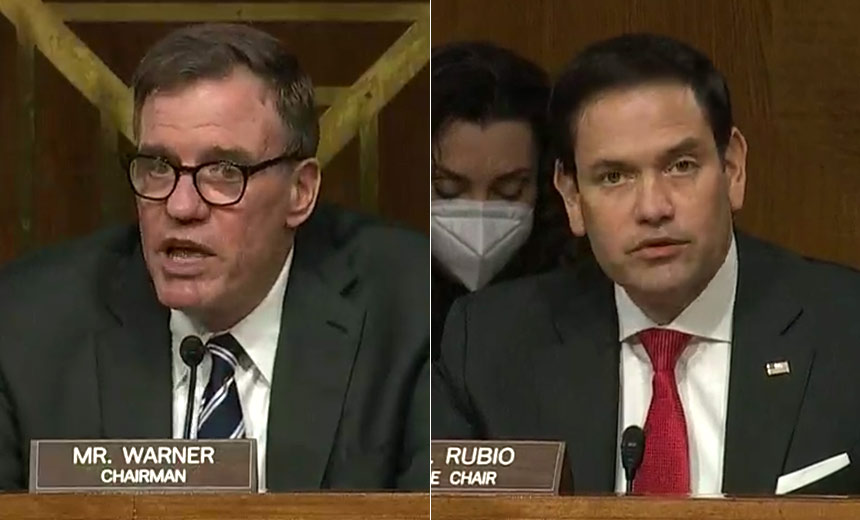
Later in the hearing, Sen. Richard Burr, R-N.C., explained that Amazon Web Services likely hosted “most” of the attackers’ secondary command-and-control infrastructure, which raised questions about how much Amazon and its executives have revealed about what they know, but also how nation-state hackers have continued to compromise infrastructure within the United States and used these services as a base for their attacks.
“Now, I feel like we’re having a cyberattack déjà vu here, whether it is the Russian hack of the DNC in 2016, North Korea and Sony or the current supply chain hacks,” Burr said. “We constantly see foreign actors [compromising] domestic infrastructure for the command-and-control to hide the nefarious traffic in legitimate traffic. The problem is that we don’t have the ability to survey the domestic infrastructure. So what should the U.S. government’s role be in identifying these types of attacks?”
During the hearing, other senators noted that Amazon should be asked again to testify and that the committee could issue a subpoena, if necessary.
2. Hackers Conducted a ‘Dry Run’
During his testimony explaining how parts of the supply chain attack worked, FireEye CEO Kevin Mandia revealed that the attackers appear to have conducted a “dry run” in October 2019 to test their techniques.
“They put an innocuous build in to make sure that it made it to the [production] environment,” Mandia said, adding that 100 of his company’s engineers spent more than 10,000 man-hours investigating how the initial breach happened and how that led them to the SolarWinds server.
In looking at the size and scope of the attack, Sen. Kirsten Gillibrand, D-N.Y., asked Microsoft’s President Brad Smith how his company had concluded that 1,000 developers worked on the campaign.
Smith explained that not all the developers worked on the initial attack and many were assigned to create some of the secondary malware used once the initial backdoor, called “Sunburst,” was sent and deployed by SolarWinds’ customers.
“This was a very elaborate and very patient, persistent set of work,” Smith said.
3. Russia’s Motives Are Not Yet Completely Clear
Witnesses told the Senate panel that a Russian-backed hacking group likely spearheaded the attack although none made a definitive attribution. Smith testified: “We’ve seen substantial evidence that points to the Russian foreign intelligence agency and we have found no evidence that leads us anywhere else.”
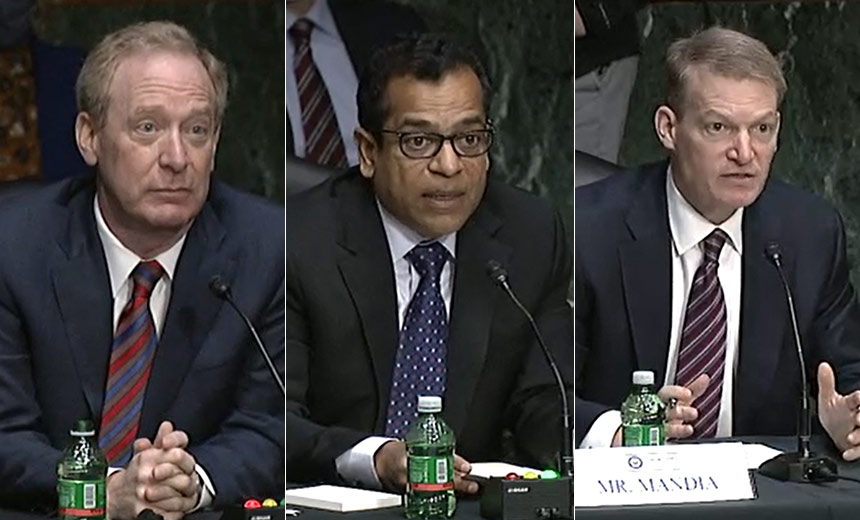
The testimony from Smith, Mandia and others backed the initial conclusions of the federal agencies investigating the attack that the hackers involved are likely based in Russia (see: SolarWinds Attack: Pointing a Finger at Russia).
During the hearing, some lawmakers questioned the exact motives for the attacks. Originally, reports indicated that the hackers had been conducting a cyberespionage campaign designed to collect data, such as email chatter. Smith noted that the attack itself was “reckless” and could have caused much more serious damage.
When Rubio spoke at the beginning of the hearing, he said that there is no evidence to date that the attack was more than a cyberespionage campaign and that drawing conclusions at this point was not justified.
“While I share the concern that an operation of this scale with a disruptive intent could have caused mass chaos, those are not the facts that are in front of us,” Rubio said. “Everything we have seen thus far indicates that this was an intelligence operation – a rather successful one – that was ultimately disrupted.”
4. More Information Sharing Is Needed
During Tuesday’s hearing, those testifying agreed with many of the committee members that more needs to be done to share intelligence when a major data breach occurs.
This could include updating the 2015 Cybersecurity Information Sharing Act to make it easier to share intelligence and provide protection for what Mandia called “first responders” who respond to breaches and gather the initial intelligence.
“There has got to be a way for folks who are responding to breaches to share data quickly to protect the nation, protecting industries, and that would require defining what a first responder is,” Mandia said. “If you are trying to figure out what happened to unauthorized or unlawful access to a network, you are a first responder … and first responders should have an obligation to share threat intelligence to some government agency without worrying about liabilities and disclosures, so we’re getting intel into people’s hands so that they can figure what to do about it.”
After the hearing, Tom Kellermann, who is head of cybersecurity strategy for VMware and a member of the Cyber Investigations Advisory Board for the U.S. Secret Service, agreed that lawmakers need to do more to ensure that private and public entities are sharing intelligence.
News Editor Doug Olenick contributed to this report.