Recently Patched Confluence Vulnerability Exploited in the Wild
Hackers started exploiting a vulnerability in Atlassian’s Confluence enterprise collaboration product just one week after the availability of a patch was announced.
Atlassian informed customers on August 25 that Confluence is affected by a critical vulnerability — described as an OGNL injection issue — that can allow remote attackers to execute arbitrary code on impacted Confluence Server and Data Center instances.
The flaw, tracked as CVE-2021-26084, can in some cases be exploited without authentication. Patches are included in versions 6.13.23, 7.4.11, 7.11.6, 7.12.5 and 7.13.0.
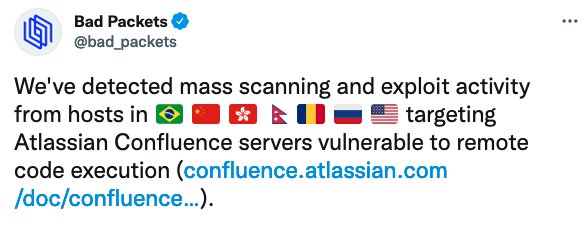
On August 29, researchers said it was easier than expected to reproduce the exploit. On September 1, cybersecurity companies started seeing internet scans aimed at identifying vulnerable systems, as well as exploitation attempts.
Threat intelligence company Bad Packets has observed attacks exploiting CVE-2021-26084 to deliver cryptocurrency miners.
After the first in-the-wild exploitation attempts were spotted, researchers released a technical analysis of the vulnerability and proof-of-concept (PoC) exploit code, which will likely lead to even more threat groups adding the Confluence vulnerability to their arsenal.
Government cybersecurity agencies started issuing alerts for CVE-2021-26084 after the first exploitation attempts were observed.
Both profit-driven cybercriminals and state-sponsored threat actors have been known to target vulnerabilities in Atlassian products.
Related: Atlassian Patches Critical Vulnerability in Jira Data Center Products
Related: Researchers Detail Exploit Chain for Hijacking Atlassian Accounts
Related: AESDDoS Botnet Targets Vulnerability in Atlassian’s Confluence Server