Nigerian Gang Asks for Insider Help to Plant Ransomware
Fraud Management & Cybercrime
,
Governance & Risk Management
,
Insider Threat
Researchers Learn Details During a Telegram Chat With an Attacker
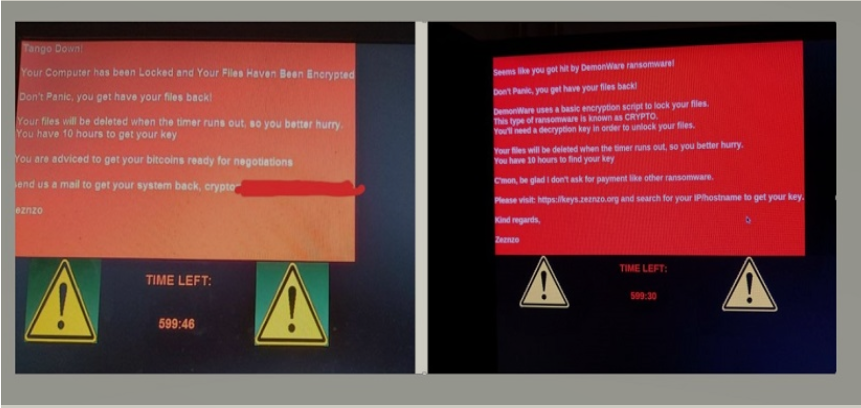
A Nigeria-based ransomware gang is conducting a campaign that dangles a $1 million bribe – or a portion of any ransom collected – to employees of targeted organizations if they will install DemonWare ransomware on their corporate network, Abnormal Security reports.
The security firm says it blocked a number of emails containing the offer, tracking them to a Nigerian.
See Also: Live Webinar | Password Management: Securing Hybrid Work for the Long Haul
“We constructed a fictitious persona and reached out to the actor on Telegram to see if we could get a response,” says Crane Hassold, director of threat intelligence with Abnormal Security. “It didn’t take long for a response to come back, and the resulting conversation gave us an incredible inside look at the mindset of this threat actor.”
Hassold adds: “Based on our conversation with the actor, he claimed to have successfully deployed the ransomware against three companies; however, we haven’t been able to verify his claims.”
Getting in Touch
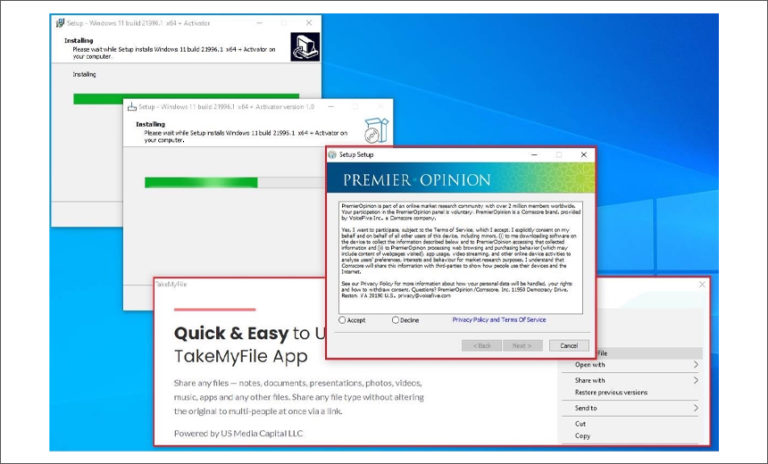
The campaign’s operators were quick to react when a researcher answered their email with a reply through Telegram. An attacker responded in about 30 minutes, asking about whether the researcher had access to his employer’s Windows server, Hassold says. The researcher replied “yes” and was rewarded with two links leading to the sharing sites WeTransfer or Mega.nz.

“Based on an analysis of the file [examined by Hassold’s team], we were able to confirm that it was, in fact, ransomware,” Hassold notes.
Abnormal Security says the hacker confirmed he was Nigerian. But he also claimed he had developed DemonWare, even though this ransomware is freely available on GitHub.
“In this case, our actor simply needed to download the ransomware from GitHub and socially engineer someone to deploy the malware for them,” he says. “This demonstrates the appeal of ransomware-as-a-service, as it lowers the barrier for less technically sophisticated actors to get into the ransomware space.”
Finding the Insider
During Abnormal Security’s lengthy conversation with the attacker, the researchers asked how the attacker singled out people for the opportunity to participate in an attack. The attacker revealed that he used the social media site LinkedIn to find victims and said that spreading ransomware was not his first intention.
“According to this actor, he had originally intended to send his targets – all senior-level executives – phishing emails to compromise their accounts, but after that was unsuccessful, he pivoted to this ransomware pretext,” Hassold says.

“Many email-based cyber threats today have become less technically sophisticated because email defenses have gotten quite good at stopping attacks using things like malicious payloads, but aren’t very good at detecting more basic social engineering attacks,” Hassold says. “This is why attacks like business email compromise have become so common today.”
Abnormal Security says this campaign is a logical extension of the business email compromise attacks carried out from Nigeria.
“While the approach seems amateurish, I think it actually fits within the framework of tactics this actor has become accustomed to. Like many Nigerian threat actors, social engineering has been a core strategy for decades, so it makes sense that this actor would use those techniques even when trying to deploy something more technically sophisticated, like ransomware,” Hassold says.
The Insider Threat
Attempting to use an insider to wage a ransomware attack or other malware intrusion is relatively rare.
But in July 2020, Egor Igorevich Kriuchkov conspired to extort $4 million from electric car manufacturer Tesla by trying to entice an employee to plant malware capable of exfiltrating data in the company’s network. Kriuchkov pleaded guilty to the scheme in March (see: Russian Pleads Guilty in Tesla Hacking Scheme).