Live Webinar | Data Classification: The Foundation of Cybersecurity ComplianceWebinar.
Thank you for registering with ISMG
Complete your profile and stay up to date


Cyber operatives affiliated with the Russian Foreign Intelligence Service (SVR) have switched up their tactics in response to previous public disclosures of their attack methods, according to a new advisory jointly published by intelligence agencies from the U.K. and U.S. Friday. “SVR cyber operators appear to have reacted […] by changing their TTPs in an…

SolarWinds told Congress that using the password ‘solarwinds123’ was an intern’s mistake. A key researcher told Insider the log-in information was posted publicly on GitHub for years. Cybersecurity experts say the issue appears to represent more than an intern’s weak password. Visit the Business section of Insider for more stories. Two SolarWinds CEOs told the…

Executive Summary This vulnerability is currently undergoing analysis and not all information is available. Please check back soon to view the completed vulnerability summary Informations Name CVE-2021-32655 First vendor Publication 2021-06-01 Vendor Cve Last vendor Modification 2021-06-01 Security-Database Scoring CVSS v3 Cvss vector : N/A Overall CVSS Score NA Base Score NA Environmental Score NA…

Softpedia News / Security 8. June 2021 This article has been indexed from Softpedia News / Security The US Department of Justice charged a woman for her alleged involvement as a programmer in a cybercrime group that helped develop TrickBot, according to The Hacker News. The woman in question, Alla Witte, nicknamed Max, of…

Today is Microsoft’s Jube 2021 Patch Tuesday, in which Microsoft had fixed Six Zero-day vulnerabilities which you should apply. In total Microsoft patched 50 vulnerabilities in this June update, among which five are noted as critical and the rest 45 are marked as important. The six actively exploited zero-day vulnerabilities are: CVE-2021-31955 – Windows Kernel…
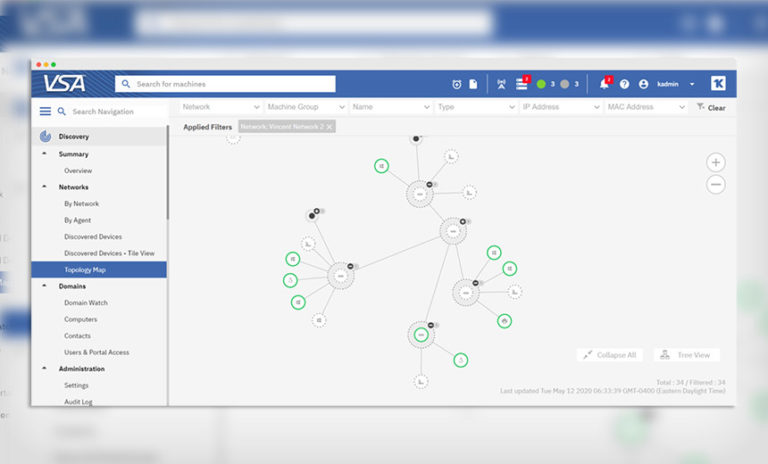
3rd Party Risk Management , Endpoint Security , Fraud Management & Cybercrime Software Vendor Quiet on Whether It Might Pay for REvil’s Full Decryption Tool Jeremy Kirk (jeremy_kirk) • July 6, 2021 Screenshot of Kaseya’s remote IT management software VSA, which was compromised by ransomware attackers. (Source: Kaseya) Kaseya said late Monday that…