Latvian woman Charged For Her Role In Creating And Deploying Trickbot Malware
In a press release, the US Department of Justice declared it had charged a Latvian woman for her part in reportedly creating and deploying the Trickbot malware, which infected millions of devices, targeting schools, healthcare institutions, public utilities, and governments.
The agency claims that Alla Witte was part of a criminal organization known as the Trickbot Group that operated in Russia, Belarus, Ukraine, and Suriname, and primarily targeted victim computers belonging to organizations, entities, and individuals, including those in the Northern District of Ohio and elsewhere in the United States.
She supposedly helped develop the malware which was used to authorize ransomware requests and payments. As stated by the DOJ, the victims would receive a message that their devices were encrypted, and were instructed to purchase special software via a bitcoin address connected to the Trickbot Group in order to have their files decrypted.
Witte, who previously lived in Paramaribo, Suriname, was arrested on Feb. 6, in Miami, Florida. According to the Justice Department, she was arraigned Friday in federal court in Cleveland.
Deputy Attorney General Lisa O. Monaco stated:
Trickbot infected millions of victim computers worldwide and was used to harvest banking credentials and deliver ransomware. The defendant is accused of working with others in the transnational criminal organization to develop and deploy a digital suite of malware tools used to target businesses and individuals all over the world for theft and ransom.
These charges serve as a warning to would-be cybercriminals that the Department of Justice, through the Ransomware and Digital Extortion Task Force and alongside our partners, will use all the tools at our disposal to disrupt the cybercriminal ecosystem.
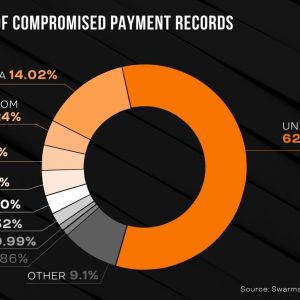
As stated by the agency, the Trickbot malware was created to catch online financial login credentials to obtain access to other personal data such as credit card numbers, emails, passwords, Social Security numbers, and addresses
According to the charges, the woman and her partners have stolen funds and private information from unknowing victims, including organizations and their financial institutions, across Australia, Belgium, Canada, Germany, India, Italy, Mexico, Spain, Russia, the United States, and the United Kingdom, exploiting the Trickbot malware.
Witte also allegedly provided code to the Trickbot Group that monitored and tracked authorized users of the malware and developed tools and protocols to store stolen login credentials.
Initially emerging as a banking trojan in 2014, Trickbot malware has increasingly been employed by threat actors to spread malware attacks, particularly in the wake of the takedown of the Emotet botnet.
As of January 27th, 2021, Emotet botnet’s infrastructure has been taken down, effectively disrupting the spread of Emotet malware. This result was achieved as part of an international coordinated operation led by Europol and Eurojust. Law enforcement agencies from all across Europe, including Germany, Ukraine, France, Lithuania, the Netherlands, and the UK collaborated with authorities from the United States to take control of the cybercrime rink’s zombie computer servers.
After gaining control of the Emotet server earlier in the same week, law enforcement managed to take down the entire botnet.
In total, Witte has been charged in 19 counts of a 47-count indictment. If convicted, she could face up to 87 years in prison.
According to ZDNet, information about the other individuals charged in the indictment is private at the moment.