Kaseya cyberattack: MSPs spared from ransoms – Security
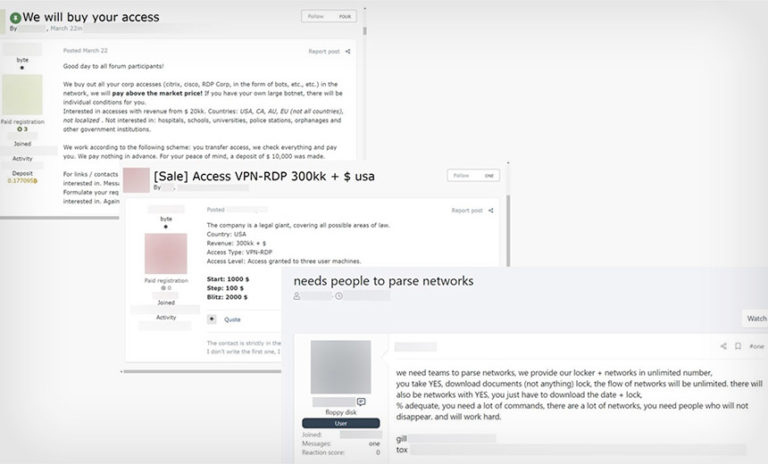
The ransomware gang who attacked Kaseya locked down systems and demanded ransom payments from end user organisations while passing over MSPs and Kaseya itself, according to Kaseya CEO Fred Voccola.
Voccola told CRN USA the ransomware attacker sought money only from end customers rather than the approximately 50 MSPs who had been compromised through an on-premises version of Kaseya’s VSA remote monitoring and management tool. The REvil ransomware group demanded US$50,000 from smaller victims and US$5 million from larger ones, according to The Washington Post.
“These attacks have gotten much more sophisticated,” Voccola said Saturday afternoon. “These are smart people.”
Kaseya’s technical teams are working with impacted end users customers and MSPs around the clock and are specifically helping them navigate the cyber insurance process as well as assisting from a legal perspective when it comes to dealing with federal and state authorities. The company has also been able to assist and provide value to victims when it comes to the technical response, Voccola said.
“We have a lot of resources as a company, and a lot of our customers don‘t,” Voccola said. “So, a lot of times, it’s just they need to talk to a lawyer, they need someone to review their logs. Anything that we can do to help, [we will],” said Voccola, specifically citing the company’s big internal legal department, external legal resources, and backup and recovery experts.
For the 50 MSPs impacted in the cyberattack, Voccola said only a subset of their end customers were subsequently hit, meaning that not every device under the management of those MSPs was ultimately ransomed. That’s different from what Huntress Senior Security Researcher John Hammond found, who said the ransomware spread from the compromised MSP through the VSA and into all the MSP’s clients.
The vulnerability exploited by the ransomware gang was only available in a small instance of Kaseya’s 6,500 on-premise customers, according to Voccola. He declined to comment on whether the impacted MSPs had two-factor authentication and other security controls and best practices in place. Two-factor authentication is turned on by default in Kaseya’s VSA product, Voccola said.
Voccola said Kaseya has identified the vulnerability and devised a patch and is currently having two third-party organisations conduct penetration tests on the patch as well as carrying out its own quality assurance efforts. He anticipates access to both the on-premises and SaaS versions of VSA will be restored at the same time. Kaseya has 37,000 VSA customers, none of which were compromised through the tool’s SaaS version.
“The biggest lesson I’ve learned is trust the process and don’t take risks,” Voccola said. “A day of downtime – or 36 hours of downtime – is much better than someone getting ransomed.”
Voccola declined to comment on whether any end customers paid the ransom and wasn’t sure how many end customers were actually ransomed since Kaseya isn’t able to see on its own how many end user organizations are served by a single MSP. Kaseya does have a cyber insurance policy in place, but Voccola said he isn’t sure at this point what the economic impact of the ransomware attack will be.
“The last thing that we‘re thinking about right now is how much money this is going to cost us,” Voccola said. “We have to make sure we take care of these 50 customers.”
A Kaseya MSP impacted by the cyberattack, who did not want to be identified, said his customers are still not able to get online in the wake of the ransomware attack.
“We are still dealing with this ransomware crises,” he said. “Our customers rely on the Kaseya product to do their work. So right now, none of our customers can get online. Kaseya told us last night they would have hosted customers up by 9 am today. Now they expect to have us back online tonight at 8 pm. We are hopeful.”
The MSP said the Kaseya attack is yet another moment of reckoning for MSPs grappling with a constant barrage of security attacks.
“MSPs are in the public eye and are on notice,” he said. “We are the protectors of our customer’s data- the holders of the keys and we rely on the MSP platform vendors like Kaseya to protect us. This isn’t working. We need to do something more as MSPs to make sure that our customers are not impacted by an attack like this.
The MSP said the MSP community needs to band together to come up with a plan to better protect customer’s data. “Ransomware and cyberattacks are at a pandemic level,” he said. “It has never been worse, and it appears to be getting even worse with each passing day. Nobody is safe right now.”
All that said, the MSP credited Kaseya with doing a good job of being transparent and communicating on the steps it is taking to get MSPs and their customers back online.
“Kaseya has done all the right things,” he said. “We are waiting for a full report once this is resolved. We are really fortunate that this happened on the July 4 weekend when many of our customers are not working. If this had been a regular work week, it would have been a much bigger disaster.”
Steven Burke contributed to this report.