IoT Security Dangers Loom as Office Workers Return
Business Continuity Management / Disaster Recovery
,
COVID-19
,
Cybercrime
Researchers: Home and Office Connected Devices Vulnerable to Attack
As corporate America begins to ask employees to come back to their offices starting in the fall, cybersecurity teams have a huge task before them to ensure their work environment is safe – particularly when it comes to internet of things and other connected devices.
See Also: Live Webinar | Improve Cloud Threat Detection and Response using the MITRE ATT&CK Framework
The problem now facing organizations started in March 2020, when IT and cybersecurity teams began setting up workers to operate from home, and few had time to worry about the IoT devices left behind, says Mark Ostrowski, head of engineering for security firm Check Point.
“Early in the pandemic, the focus of security was to transform their workforce connectivity (remote access), which assumed the primary method of access to corporate functions. Secondarily to that transformation was implementing and shifting application load to the cloud,” Ostrowski says.
And this rush to the exits opened the doors wide open for cybercriminals.
A recent report by Zscaler’s ThreatLabz team notes that during the past 18 months, attackers launched unprecedented waves of attacks against IoT devices that office workers essentially abandoned when they started working from home. These devices now have to be secured along with all the devices that workers used at home or bought while away from their office desk.
The devices attackers targeted included obvious office equipment such as printers and IP cameras, but stretched to smart TVs and automobiles. Making it even easier for a malicious actor to intercept and swipe data is the fact that 76% of all communication taking place from and between these devices is through unencrypted plain text channels, Zscaler says.
Deral Heiland, principal security research for IoT at Rapid7, says the attack surface is even wider regarding IoT devices in a modern corporate setting.
“Often IoT devices seem to have crept into the environment over the years, such as office cafeteria room appliances, coffee makers, toasters let alone the standard business technology including conferencing systems, TVs, printers and security cameras,” he says.
Heiland notes that when offices shut down, it would have been the perfect opportunity for IT teams to redesign networks to support IoT technologies in the workplace, but understandably this did not happen. This task, however, might be accomplished now, he says.
Heading Off to Work
Ensuring the safety of an organizations network and data as people begin return means a great deal of preparation work has to be done with the first step cataloging all the IoT devices currently in use the organization and assigning ownership which has always been lacking in many organizations, Heiland says.
“Segmentation of all IoT technology, most if not all of these IoT based technologies should be segmenting into VLANs so they cannot gain access to the business network,” he notes.
The fact that offices were unused spurred some changes that further endangered the company from a cybersecurity perspective, says Ostrowski.
Check Point notes the company had one customer that installed more than 6,000 connected light bulbs to gain energy efficiency in empty offices; however, the security team was not aware of this initiative.
“The potential vulnerability of IoT is very clear; these devices are more numerous than user devices, they are mostly unmanaged and run firmware based on platforms that are largely exploitable, such as Android and Linux,” Ostrowski says. “Identifying, classifying and assuring that these devices have the least amount of access required, zero trust, are the key steps.”
In areas of critical nature, such as in the medical field, air-gapping IoT is very important such as industrial controls, medical IoT, he says.
Other recommendations made by Rapid7’s Heiland include:
- Ensure all current and future IoT technology are part of the corporate patch management program;
- Implement an incident detection and response program that also includes IoT devices;
- Monitor communication to and from these IoT devices to allow identification of compromised devices.
“For example, printers and also some security cameras regularly do not have passwords properly configured on them, creating an easy avenue, if the organization is breached, for malicious actors to hide and pivot on a network with a low chance of being detected,” Heiland says.
Bringing in Danger
The IoT devices intentionally added to a network are only part of the problem facing IT teams. People working from home not only bought additional IoT devices to help them work more efficiently in their new location, but all have been operating company laptops and phones across home and other networks that may or may not be fully secure.
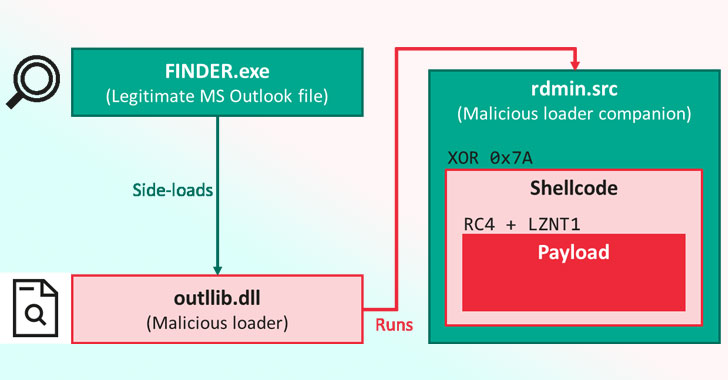
Viral Ghandi, senior security researcher for mobile and IoT with Zscaler, notes that home networks are generally less secure, so there is every possibility attackers took the opportunity to plant malware while the devices were away from their office networks.
“Combating this problem requires a combination of visibility, architecture, and policy enforcement,” says Ghandi. “IT teams need visibility into the unsanctioned devices in their environment and should be inspecting all encrypted and unencrypted traffic going to the internet. Utilizing zero trust is the only way to ensure that these devices don’t leave them vulnerable to data exposure.”
Ostrowski adds: IoT and mobile device security should be top of mind for all security teams. These devices are quickly becoming the dominant devices on networks at home and work so the same level of visibility and prevention need to be in place as do with traditional network devices.
Empty Offices Attacked
As millions of workers streamed out of their office in March 2020 and began to work from home, cybercriminals quickly moved in, attacking the now uncountable IoT devices left behind.
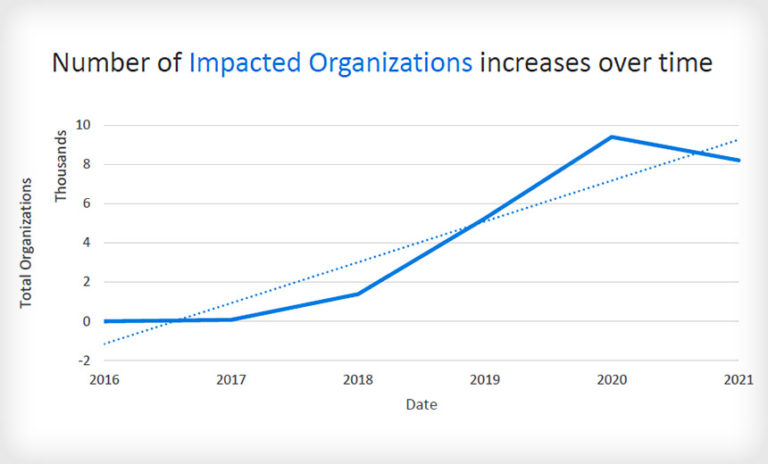
Zscaler reports that during 2020, the amount of IoT malware on corporate networks increased 700% year-over-year, despite much of the global workforce working from home. This equated to 833 IoT attempts to place malware on a device per hour, according to Zscaler’s tracking.
Almost all of the attacks were attempts to pull these now unused devices into botnet armies.
All aspects of the attacks were highly concentrated in just a few areas:
- 97% of the malware tracked belonged to the Gafgyt and Mirai botnet families;
- Devices in technology (40%), manufacturing (29%), retail and wholesale (24%), and healthcare (5%)industries accounted for 98%of IoT attack victims;
- Attackers from the U.S. China and India were responsible for incidents;
- Most victims were located in Ireland, the U.S. and China.