Facebook Data Exposure: Lessons to Learn
Governance & Risk Management
,
Identity & Access Management
,
IT Risk Management
Experts Advise Organizations to Check Password Reset Policies, Take Other Steps

The revelation that 533 million previously stolen Facebook account records have been made public on a darknet forum should inspire organizations to take aggressive action to further protect customer data security, some security experts say.
See Also: Live Webinar | Attacks on Cloud Infrastructure
Although the data posted on the forum is several years old, it still poses risks because so much of it, including telephone numbers, is likely still valid, says Lorrie Cranor, director of the Cylab Security and Privacy Institute at Carnegie Mellon University.
“This breach did not leak passwords or financial account information, but it leaked information that can certainly be of use to identity thieves and make it easier for them to impersonate people and compromise their accounts,” Cranor says. “Organizations should check their password reset processes and make sure that the breached info alone is not enough to reset a password and take over someone’s account. Consumers should be using two-factor authentication whenever it is available. This is just another reason why that is a good idea.”
Chris Clements, a vice president at the security firm Cerberus Sentinel, says organizations should devise better ways of proving customers’ identities that avoid relying on data commonly stolen in data breaches and posted on criminal forums.
“There are technical solutions to these problems, such as using rotating code, time-based, one-time passwords that ensure that identifying information can’t be stolen and reused. But the challenge is large-scale implementation,” Clement says. “It’s simply not currently feasible to assume everyone has access to a smartphone to run an authenticator app, and likewise for distributing purpose-based devices.”
Tim Mackey, principal security strategist at the Synopsys Cybersecurity Research Center, says it’s also important for organizations to minimize the amount of data they collect from their customers. And customers, in turn, should “hold those with whom they share their data accountable for its safekeeping,” he says.
Brian Honan, CEO and principal consultant at Dublin-based BH Consulting, tweeted that there should be pushback against those who want social media firms to collect even more information.
This breach also highlights why people calling for social media networks to get more personal data for age verification purposes don’t understand the risks https://t.co/81Jc8l2qQu
— BrianHonan #BLM He/Him (@BrianHonan) April 4, 2021
Meanwhile, organizations in all sectors must train their staff members to spot social engineering scams that take advantage of breached data, adds James McQuiggan, security awareness advocate at KnowBe4.
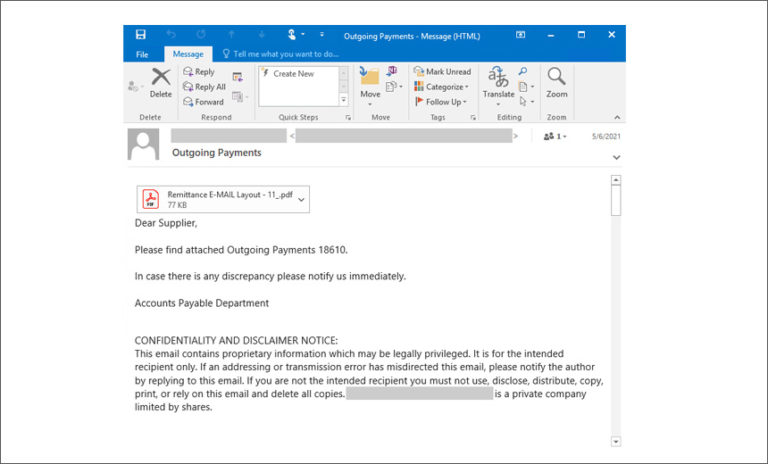
The Discovery
Alon Gal, chief technology officer at Hudson Rock, discovered the Facebook database in January on a darknet forum where it was offered for sale. A Telegram bot allowed anyone to search the database and find phone numbers linked to accounts. Gal says that on Saturday the attacker removed the paywall, leaving the data open to anyone who could access the forum.
The half-billion accounts for which data was exposed represent users in 106 countries. Information in the database includes phone numbers, Facebook IDs, names, locations, past locations, birthdates and, in some cases, email addresses, account creation dates, relationship status and the biographical information submitted by the account owners, Gal says.
Facebook says the data was previously reported as exposed in 2019, when the attacker harvested it by exploiting a since-patched vulnerability.
Facebook’s Responsibility
Sam Curry, chief security officer at Cybereason, says that in the wake of the posting of Facebook data on a darknet forum – and several other earlier data security incidents – the social media giant should take bold action.
“This isn’t the time for Facebook to play the victim, and they really only have two options: Be the hero or villain,” Curry says. “Many see Facebook as an industry villain and their minds won’t be changed. But this is another time for Facebook to face its challenges head-on, update users on their privacy policies and continue doing everything possible to protect their data.”
In 2018, 30 million Facebook accounts were breached, with 14 million accounts having an extensive amount of information exposed (see: Facebook Clarifies Extent of Data Breach).
Facebook also had 87 million user profiles collected in 2015 by Cambridge Analytica, which reportedly used the data to develop psychographic profiles for use in planning political advertising campaigns. The company, which worked for a few months for President Donald Trump’s 2016 campaign, filed for U.S. bankruptcy in May 2018 (see: Facebook Agrees to Pay UK Fine in Cambridge Analytica Case).