Compromised Website Images Camouflage ObliqueRAT Malware
.
The ObliqueRAT malware is now cloaking its payloads as seemingly-innocent image files that are hidden on compromised websites.

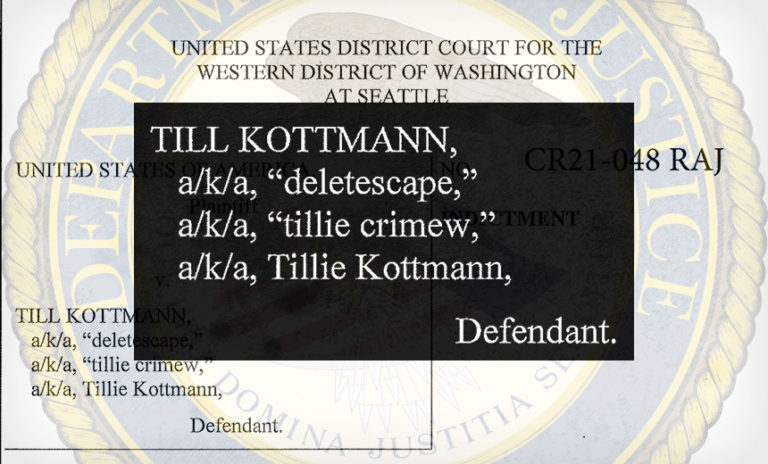
Application Security , Cybercrime , Device Identification Swiss Citizen Allegedly Leaked Victims’ Stolen Data, Including Source Code Jeremy Kirk (jeremy_kirk) , Mathew J. Schwartz (euroinfosec) • March 19, 2021 A Swiss national who recently highlighted flaws in internet-connected Verkada surveillance cameras has been charged with hacking. See Also: Top 50 Security Threats …

A distributed denial-of-service (DDoS) extortion group has blazed back on the cybercrime scene, this time under the name of “Fancy Lazarus.” It’s been launching a series of new attacks that may or may not have any teeth, researchers said. The new name is a tongue-in-cheek combination of the….

Easy to redeem and hard to trace, gift cards remain a hot commodity in the criminal underground A cybercriminal has sold almost 900,000 gift cards and over 300,000 payment cards on a top-tier cybercrime forum on the dark web. The total value of the cards was claimed to be some US$38 million. The hacker probably…
Researchers at cybersecurity firm Check Point discovered that many Android applications publicly expose sensitive user data through misconfigured third-party services. The research involved the analysis of 23 Android applications and revealed issues related to real-time databases, cloud storage keys, and push notifications. The exposed data, which pertains to more than 100 million Android users, includes…

E Hacking News – Latest Hacker News and IT Security News 29. June 2021 This article has been indexed from E Hacking News – Latest Hacker News and IT Security News Earlier this month, Microsoft signed a driver called Netfilter that turned out to be a malicious network filter rootkit. Krasten Hahn, a G…

Feb 23 (Reuters) – Top executives at Texas-based software company SolarWinds, digital giant Microsoft and cybersecurity firms FireEye and CrowdStrike are expected on Tuesday to defend their companies’ responses to a sprawling series of breaches blamed on Russian hackers when they face the U.S. Senate’s Select Committee on Intelligence. The four are expected to argue…