US Census Bureau Criticized for Handling of Breach
Governance & Risk Management
,
Government
,
Incident & Breach Response
OIG Report: Bureau Did Not Properly Maintain Security Logs of Incident

Following a breach of some of its servers in January 2020, the U.S. Census Bureau failed to follow standard cybersecurity practices, including properly maintaining logs of the incident to assist in an investigation, according to an inspector general’s report made public this week.
See Also: A Guide to Passwordless Anywhere
The Census Bureau also did not conduct proper vulnerability scanning of IT assets, failed to properly notify other government officials about the incident and continued to run outdated and unsupported servers even after the attack came to light, according to the report prepared by the U.S. Department of Commerce Office of Inspector General, which has oversight over the Census Bureau.
The report also notes that it took the Census Bureau’s security team two weeks to discover the breach and that only a firewall prevented the attacker from creating a backdoor into the compromised servers.
“We found that the bureau should make improvements to its cyber incident response process. Specifically, the bureau missed opportunities to mitigate a critical vulnerability, which resulted in the exploitation of vital servers,” according to the report. “Once the servers had been exploited, the bureau did not discover and report the incident in a timely manner. Additionally, the bureau did not maintain sufficient system logs, which hindered the incident investigation. Following the incident, the bureau did not conduct a lessons-learned session to identify improvement opportunities.”
The OIG made nine cybersecurity recommendations to the Census Bureau, and the bureau has either implemented or is in the process of implementing all of those.
The inspector general’s report on the Census Bureau follows a congressional report earlier this month that found seven federal agencies – the departments of State, Housing and Urban Development, Agriculture, Health and Human Services and Education and the Social Security Administration – lacked basic cybersecurity protections and policies despite warnings about these types of incidents increasing (see: Report: 7 Federal Agencies Still Lack Basic Cybersecurity).
The Census Bureau Breach
The January 2020 Census Bureau breach involved several servers used to provide certain employees with remote access to the department’s “production, development and lab networks,” according to the OIG report. These servers, however, were not connected to any systems used to conduct the 2020 Census.
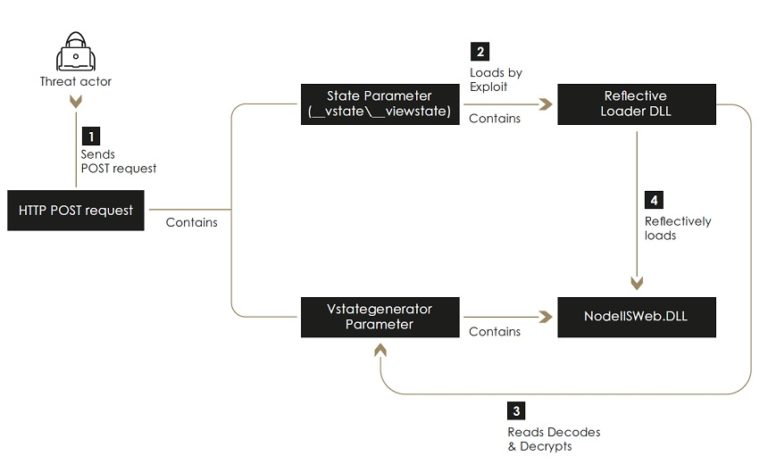
The attacker gained access to the servers using a publicly available exploit that took advantage of a vulnerability, according to the report. The attacker was then able to modify user account data within the servers, but an attempt to connect to a command-and-control server and create a backdoor in the system failed, the report notes.
The OIG did not name the exploit that the attacker utilized or the identity of the vendor that the Census Bureau used to provide employees with remote access. It notes, however, that in December 2019, the vendor released information about the vulnerability and the exploit and provided its customers, including the bureau, with steps to help mitigate the risk.
After the vendor announced the exploit, the National Institute of Standards and Technology assigned the vulnerability a “critical” rating and a member of the bureau’s Computer Incident Response Team attended a Cybersecurity and Infrastructure Security Agency briefing where the vulnerability was discussed and mitigation steps distributed.
Despite the warnings and having a mitigation plan in hand, an attacker was still able to gain access to the bureau’s servers about Jan. 11, 2020, and then attempted to create the backdoor on Jan. 13, but the bureau’s firewalls stopped the attack, the OIG report notes.
“The bureau missed opportunities to mitigate the vulnerability before being exploited, which allowed an attacker to make unauthorized changes to the remote-access servers,” according to the report. “The bureau’s firewalls blocked the attacker’s attempts to establish a backdoor to communicate with the attacker’s external command-and-control infrastructure. However, unauthorized changes were still made to the remote-access servers, including the creation of new user accounts.”
The Census Bureau did not fully discover the breach until Jan. 28, 2020, the report notes.
Security Shortcomings
The inspector general found that the Census Bureau failed to detect the breach in a timely manner and then did not conduct a proper follow-up investigation to discover what happened. Some of the security issues uncovered include:
- The Census Bureau was not using a security information and event management tool, or SIEM, to alert incident responders about suspicious network traffic. Instead, the bureau’s SIEM was used only for reactive, investigative actions.
- The servers accessed in the attack were sending incident logs to a SIEM that had been decommissioned in July 2018. Any incident logs stored locally in the servers did not contain a full record of the breach.
- The bureau’s SOC appears to have misidentified the direction of malicious traffic within the network and concluded that the attack had been blocked. In fact, the traffic showed one of the remote access servers attempting to communicate with a known malicious IP address.
- The bureau was not running vulnerability scanning of the remote access servers despite government and departmental policies.
- While the bureau migrated the remote access capabilities to newer hardware after the intrusion, it continued to run the older servers until February of this year even though they were no longer supported by the vendor.
- The bureau never conducted a “lessons learned” exercise following the incident.
The inability of the bureau’s security teams to track the logs and the fact that the logs were sent to a decommissioned SIEM show its “change control” processes were lacking, says Jake Williams, a former member of the U.S. National Security Agency’s elite hacking team.
“We recommend that clients configure alerting for their log aggregators – SIEM systems – so they are immediately alerted if logs are not being delivered,” says Williams, who is now the co-founder and CTO at BreachQuest. “If that alerting isn’t available in their log aggregator, analysts can regularly query logs from random systems to ensure their delivery.”
Andrew Barratt, managing principal for solutions and investigations at the consulting firm Coalfire, notes that the inspector general report hints that the Census Bureau might not have enough funding to fulfill all its security needs.
“The lack of access logs, monitoring and out-of-date systems perhaps shows where budgets have been trimmed and unfortunately created a false economy for the tax dollars spent,” Barratt says. “This is usually an indication of a technical-first approach to defense but lacking in a broader, more strategic view and perhaps a lack of adoption of one of the many federally approved frameworks.”
Nine Recommendations
The OIG report made nine security recommendations:
- Implement procedures to notify relevant bureau personnel when exploits and vulnerabilities are announced.
- Review scanning lists to ensure that all IT systems and equipment are identified and cataloged.
- Ensure that all network-addressable IT assets are scanned using credentials when possible.
- Review the automated alert capabilities of the bureau’s SIEM.
- Ensure that incident responders report security incidents to the bureau’s Enterprise Security Operations Center.
- Develop procedures to handle security alerts from outside agencies, such as CISA.
- Incorporate periodic reviews of the bureau’s log system to ensure that all IT systems are properly configured.
- Update policies to ensure “lessons learned” reviews are conducted in a timely manner.
- Create plans to remove end-of-life outdated systems and equipment.