The White House Is Deciding Whether to Support a Bureau of Cyber Statistics
The White House Is Deciding Whether to Support a Bureau of Cyber Statistics


Cybercrime , Cybercrime as-a-service , Endpoint Security LockBit Ransomware Gang Takes Credit, Threatens to Release Data Doug Olenick (DougOlenick) • August 30, 2021 Bangkok Airways issued an apology late last week for a data breach that apparently compromised the personally identifiable information for an unstated number of its passengers. The LockBit ransomware gang…
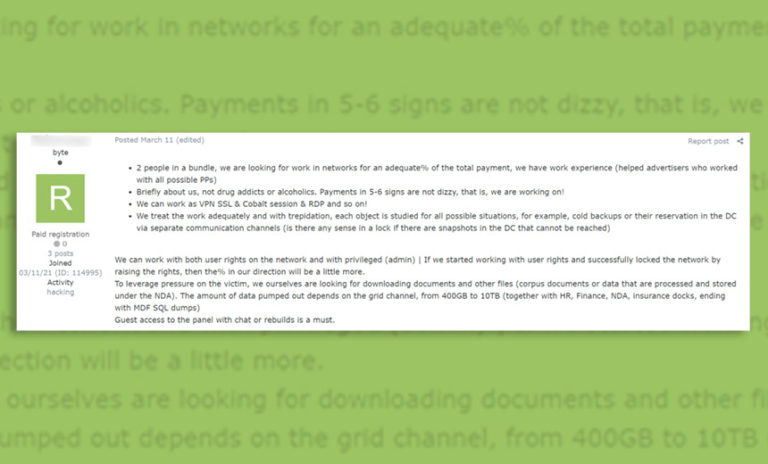
Business Continuity Management / Disaster Recovery , Cybercrime , Cybercrime as-a-service Ransomware-as-a-Service Operations Tap Expert Intrusion Specialists and Negotiators Mathew J. Schwartz (euroinfosec) • July 9, 2021 Intrusion specialists’ advertisement on a cybercrime forum seeking a ransomware operation partner to collaborate via specified terms (Source: Kela) As ransomware attacks become more prolific, their…

Experts spotted a new advanced Android spyware posing as “System Update” | IT Security News 27. March 2021 Researchers spotted a sophisticated Android spyware that implements exfiltration capabilities and surveillance features, including recording audio and phone calls. Experts from security firm Zimperium have spotted a new sophisticated Android spyware that masquerades itself as a System…

The Biden administration is preparing to issue a series of actions, including sanctions, to make it more difficult for hackers to profit off of ransomware attacks through the use of digital currency, as first reported by the Wall Street Journal on Friday. According to the Journal, the Treasury Department plans to impose these new sanctions…
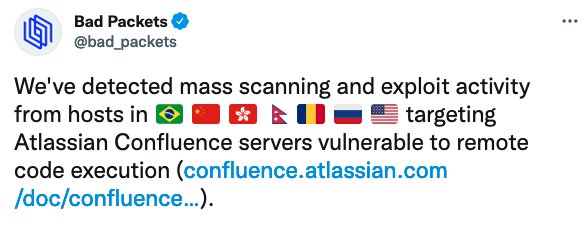
Hackers started exploiting a vulnerability in Atlassian’s Confluence enterprise collaboration product just one week after the availability of a patch was announced. Atlassian informed customers on August 25 that Confluence is affected by a critical vulnerability — described as an OGNL injection issue — that can allow remote attackers to execute arbitrary code on impacted…

Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Fraud Risk Management Federal Public Service Interior Investigating Possible Cyberespionage Campaign Akshaya Asokan (asokan_akshaya) • May 27, 2021 Belgium’s Federal Public Service Interior is investigating a possible cyberespionage campaign. Belgium’s interior ministry, Federal Public Service Interior, is investigating an attack against its network…