The Cyber Impact of Biden/Putin Summit Meeting
Cybercrime
,
Cyberwarfare / Nation-State Attacks
,
Fraud Management & Cybercrime
Experts Discuss Impact of ‘Transformational Moment’

After U.S. President Joe Biden and Russian President Vladimir Putin discussed cybersecurity issues at their Wednesday summit meeting in Geneva, security experts and analysts began sizing up what the next steps might be following what some are calling a “transformational moment.”
See Also: Live Webinar: Seeking Success by Adopting a SASE Architecture: en el idioma Español
Experts are waiting to see how Russia will respond to U.S. concerns about cyberattacks targeting its critical infrastructure. And some say the summit could serve as a catalyst for new U.S. laws, such as a national data breach reporting requirement and ransomware threat mitigation measures.
Spotlight on Cybersecurity
The Wednesday summit “brought cybersecurity home to people as a core issue,” says Chris Painter, who served as the State Department’s top cyber official during the Obama administration. “Cyber wasn’t completely off the front pages before, but for far too long this has been seen as a niche issue – and it shouldn’t be. It’s a core issue of our national security and economic security. And although these discussions have come in fits and starts in the past, this summit should be seen as a transformational moment.”

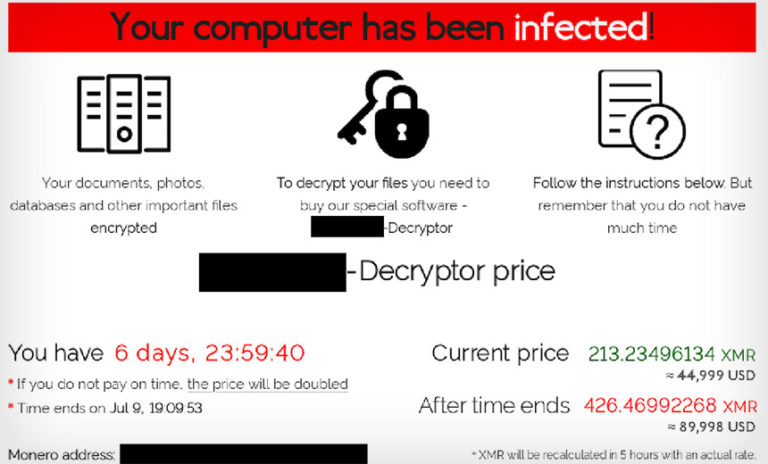
The recent flurry of ransomware attacks in the U.S. that apparently originated in Russia, including those that targeted Colonial Pipeline Co. and meat processor JBS, have put cybersecurity at the forefront of issues that world leaders must address, says Meg King, director of the Science and Technology Innovation Program at The Wilson Center, a nonpartisan think tank based in Washington.
“It’s not surprising that cybersecurity was a main talking point after the Biden-Putin meeting because it is an issue on which the two countries – if Russia cooperates – could really make a change,” King says. “This is especially true on ransomware, which has been used against the private sectors in both countries – though on different scales.”
The next steps Russia takes regarding the cybercriminal gangs that operate within its borders will set the tone for how Washington and Moscow can work together to respond to cyberthreats.
Regarding ransomware and other cyberattacks originating in Russia, “at a high level, the U.S. said: ‘This is unacceptable; it’s got to stop. And if it doesn’t stop, we’re going to take action,'” says Painter, who now serves on the board of the Center for International Security. “I think this can go in a couple of different ways … I was disappointed to see that there was practically no commitment by Putin to putting pressure on criminal groups in Russia. In his press conference, Putin basically said, ‘Nothing to see here; that’s not happening.'”
Addressing Critical Infrastructure
During the talks, Biden emphasized protecting U.S. critical infrastructure, saying that 16 sectors should be “off-limits” to cyber and other types of attacks. The Cybersecurity and Infrastructure Security Agency lists 16 industries as providing critical infrastructure.
“Of course, the principle is one thing. It has to be backed up by practice. Responsible countries need to take action against criminals who conduct ransomware activities on their territory,” Biden said after the meeting. “So we agreed to task experts in … both our countries to work on specific understandings about what’s off-limits and to follow up on specific cases that originate in other countries – either of our countries.”

In emphasizing the seriousness of the issue, Biden added that if these types of attacks continue to originate in Russia, whether or not they are sanctioned by the Russian government, the U.S. could retaliate. “And if, in fact, they violate these basic norms, we will respond with cyber,” he said.
Painter notes the two sides will now have to more clearly define what constitutes a “cyberattack” that must be prevented.
“To me, that means: Don’t do things like the Colonial Pipeline attack. Don’t do these denial-of-service attacks. Don’t do the NotPetya worm that took down Maersk in Denmark,” Painter says.
Scott Shackelford, chair of Indiana University’s cybersecurity program, stresses that the Biden administration must more precisely define what is considered critical infrastructure – such as the power grid and oil and gas infrastructure – to ensure that Russia understands what is off-limits for cyber intrusions.
“The 16 critical infrastructure sectors have been identified by the U.S. government since 1999, though the scope of these sectors has changed over time, such as with the addition of election infrastructure in 2017,” Shackelford says. “Interestingly, the idea of what constitutes ‘critical infrastructure’ is very much in the eye of the beholder – there are not 16 such sectors recognized in the EU, for example, but only seven.”
Cybercrime
Although Putin said Russia will “begin consultations” with the U.S. over a range of cybersecurity issues, he stopped short of pledging to crack down on cybercriminal activity in his nation.
Sam Curry, CSO at the security firm Cybereason, says Putin might eventually crack down on the activities of some cybercrime groups in Russia if it somehow suits his political goals.
“There is a possibility Russia would eventually give up the rogue, off-the-grid threat actors that every country has and Putin might not be aware of,” Curry says. “Only time will tell what Russia is willing to do. Keep in mind, the nature of the attackers and targets varies. There are state hackers, arms-length hackers and privateers in the ecosystem, and plausible deniability is a strategy we’ve seen before, no matter how weak the plausibility is.”
Just before the start of Wednesday’s summit, police in Ukraine, with assistance from the U.S. and South Korea, arrested several alleged members of the Clop ransomware gang. Painter notes that Russia could do the same if Putin believed it was in his best interest (see: Ukraine Arrests 6 Clop Ransomware Operation Suspects).
“Every country should have a responsibility to not be a haven for cybercrime, and we have to make sure that even we think about the larger consequences of that,” Painter says.
Catalyst for Change?
Some analysts say the Biden-Putin summit could serve as a catalyst for action on U.S. domestic policy.
Lawmakers already are crafting several bills that could include, for example, new tools for agencies such as the Department of Homeland Security to respond to ransomware attacks, as well as nationwide breach notification laws (see: What Would National Data Breach Notification Law Look Like?).
The Institute for Security and Technology’s Ransomware Task Force recently published a framework that included 48 separate provisions for curbing ransomware attacks, including developing new laws both in the U.S. and in other countries to strengthen anti-money laundering regulations.
Painter, who served on the task force, hopes that the summit will spur Congress along to address some of these issues (see: Fighting Ransomware: A Call for Cryptocurrency Regulation).
“If there’s a major data breach, especially among the critical infrastructure sectors, you should have to report it,” Painter says. “It’s hard for us to address it if we don’t even know about it, and it’s hard for us to have a handle on the problem – the scope of the problem – if we don’t know about it.”