North Korean hackers target defense industry with custom malware

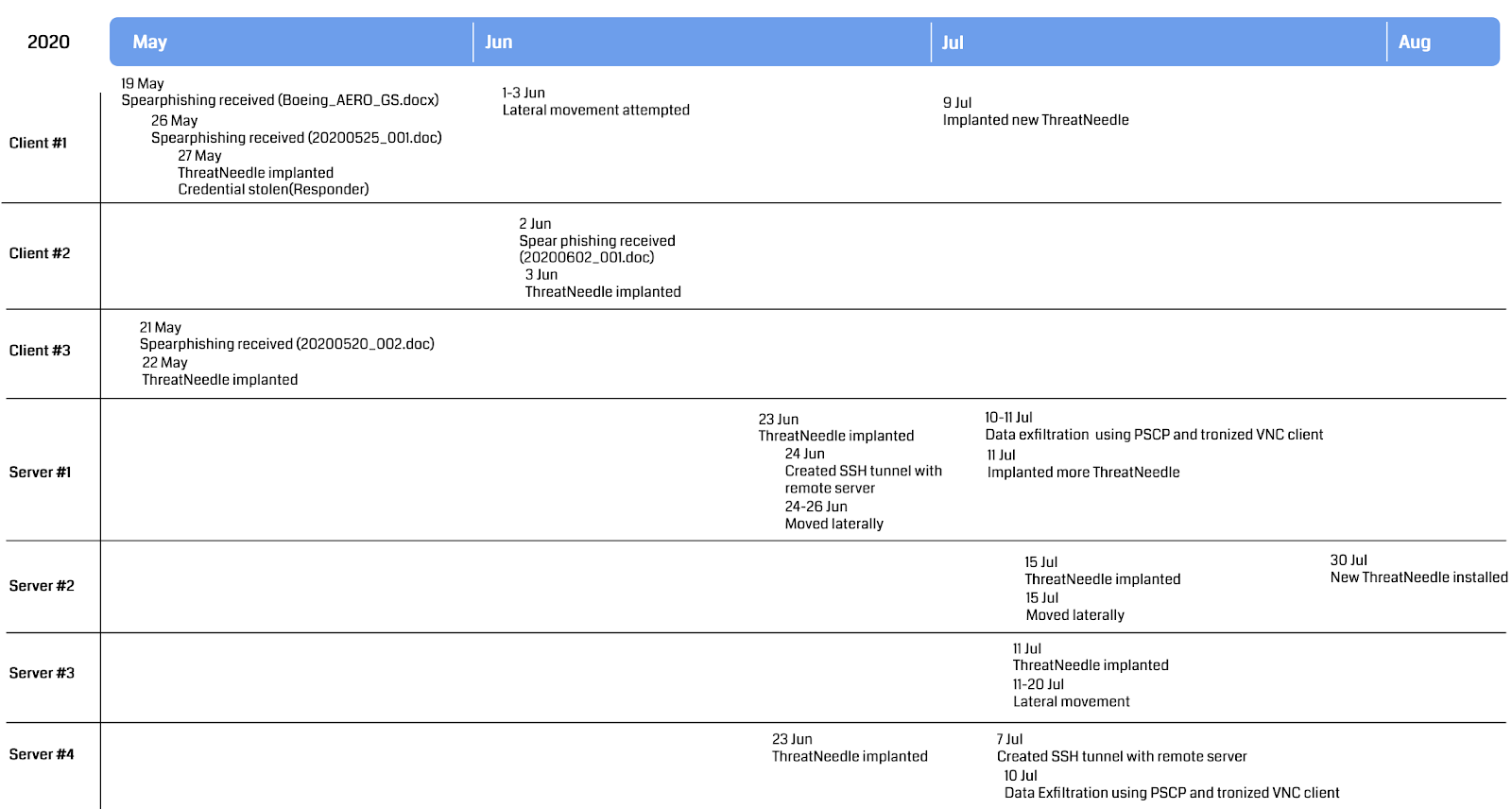
A North Korean-backed hacking group has targeted the defense industry with custom backdoor malware dubbed ThreatNeedle since early 2020 with the end goal of collecting highly sensitive information.
This espionage campaign affected organizations from more than a dozen countries and was coordinated by DPRK-backed state hackers tracked as Lazarus Group.
The attackers used COVID19-themed spear-phishing emails with malicious attachments or links as the initial access vector to the companies’ enterprise network.
After the initial compromise, they installed the group’s custom-made ThreatNeedle backdoor malware first used in 2018 in attacks targeting cryptocurrency businesses.
“Once installed, ThreatNeedle is able to obtain full control of the victim’s device, meaning it can do everything from manipulating files to executing received commands,” Kaspersky security researchers said earlier today.
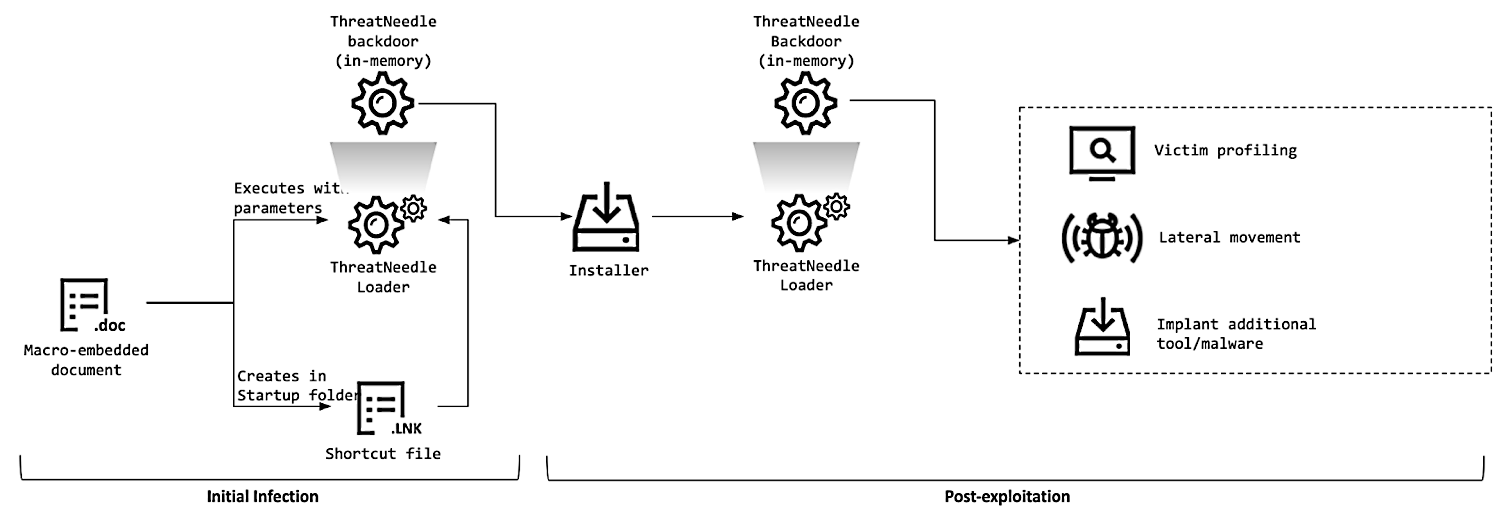
ThreatNeedle helped the Lazarus hackers to move laterally throughout the defense orgs’ networks and harvest sensitive info that got exfiltrated to attacker-controlled servers using a custom tunneling tool via SSH tunnels to remote compromised South Korean servers.
The backdoor also allowed them to bypass network segmentation and access restricted networks with mission-critical devices that didn’t have Internet access.
“After gaining an initial foothold, the attackers gathered credentials and moved laterally, seeking crucial assets in the victim environment,” Kaspersky added.
“We observed how they overcame network segmentation by gaining access to an internal router machine and configuring it as a proxy server, allowing them to exfiltrate stolen data from the intranet network to their remote server.”
Throughout their attacks, the hackers were also seen stealing documents and data from both office IT networks (from devices used for storing business and customer info) and from restricted networks (commonly used for storing and managing highly sensitive data).
The Lazarus operators took control of administrators’ workstations which later allowed them to set up malicious gateways that provided them with access to the restricted networks.
While the Lazarus Group has been known for focusing its efforts mainly on targeting worldwide financial institutions, starting with early 2020 when this campaign began, they switched their focus on “aggressively attacking” defense industry organizations.
After this move, the Lazarus hackers repurposed their ThreatNeedle malware for stealing sensitive information as part of targeted espionage attacks.
“Lazarus was perhaps the most active threat actor of 2020, and it doesn’t appear that this will change anytime soon,” said Kaspersky GReAT senior security researcher Seongsu Park.
“In fact, already in January of this year, Google’s Threat Analysis Team reported that Lazarus had been seen using this same backdoor to target security researchers. We expect to see more of ThreatNeedle in the future, and we will be keeping an eye out.”
The Lazarus hackers are also tracked as HIDDEN COBRA by the United States Intelligence Community).
They are a well-known financially motivated cybercrime group as shown by their campaigns — they hacked Sony Films as part of Operation Blockbuster in 2014 and were behind the 2017 global WannaCry ransomware campaign.