Microsoft warns Azure customers of critical Cosmos DB vulnerability

Microsoft has warned thousands of Azure customers that a now-fixed critical vulnerability found in Cosmos DB allowed any user to remotely take over other users’ databases by giving them full admin access without requiring authorization.
Azure Cosmos DB is a globally distributed and fully managed NoSQL database service used by high-profile customers, including Mercedes Benz, Symantec, Coca-Cola, Exxon-Mobil, and Citrix.
“Microsoft has recently become aware of a vulnerability in Azure Cosmos DB that could potentially allow a user to gain access to another customer’s resources by using the account’s primary read-write key,” the company told customers.
“We have no indication that external entities outside the researcher had access to the primary read-write key associated with your Azure Cosmos DB account(s). In addition, we are not aware of any data access because of this vulnerability.”
The cloud security firm Wiz’s research team, who discovered the security flaw, dubbed it ChaosDB and disclosed it to Microsoft on August 12, 2021.
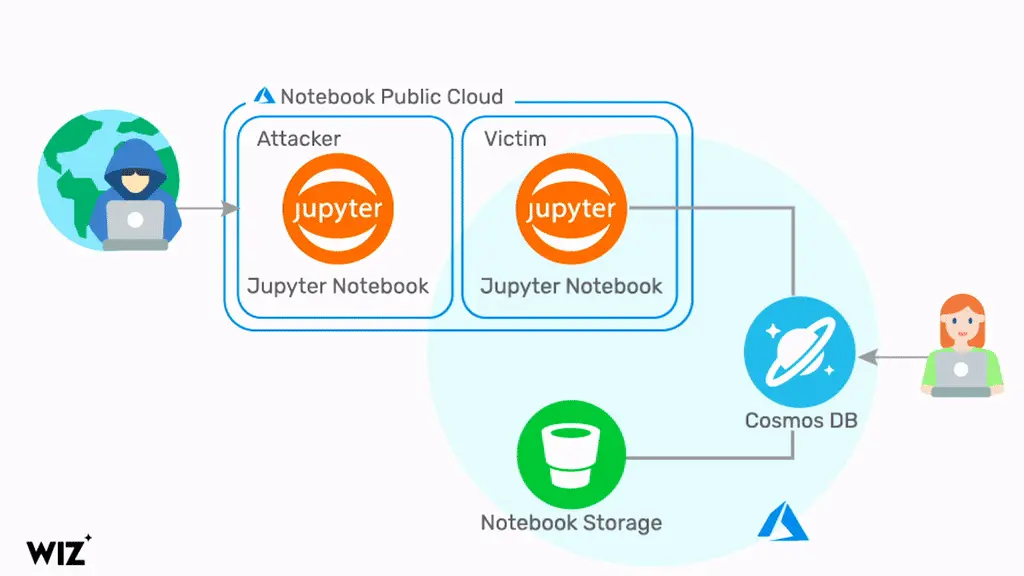
The bug enabled attackers to exploit a chain of bugs in the Jupyter Notebook feature, enabled by default and designed to help customers visualize data.
Successful exploitation enabled them to access other users’ Cosmos DB credentials, including their primary key, which provided them with complete and unrestricted remote access to Microsoft Azure customers’ databases and accounts.
“The vulnerability has a trivial exploit that doesn’t require any previous access to the target environment, and impacts thousands of organizations, including numerous Fortune 500 companies,” the researchers said.
Microsoft disabled the vulnerable entry point feature within 48 hours after receiving the report and alerted more than 30% of Cosmos DB customers about a potential security breach on August 26, two weeks after disabling the buggy Jupyter Notebook feature.
However, according to the Wiz research team, the actual number of impacted customers is likely a lot larger as it probably includes most Cosmos DB customers, given that the ChaosDB vulnerability was present and could’ve been exploited for months before their disclosure.
To mitigate the risk and block potential attacks, Microsoft advises Azure customers to regenerate the Cosmos DB Primary Keys that could’ve been stolen before the vulnerable feature was disabled.
The company also advised customers to take the following recommended actions to further secure their Azure Cosmos DB databases:
- Schedule a regular rotation and regeneration of your primary and secondary keys.
- As a standard security best practice, consider using the Azure Cosmos DB firewall and virtual network integration to control the access to your accounts at the network level.
- If you are using the Azure Cosmos DB Core (SQL) API, consider using the Azure Cosmos DB role-based access control (RBAC) to authenticate your database operations with Azure Active Directory instead of primary/secondary keys. With RBAC, you have the option to completely disable your account’s primary/secondary keys.
- For a complete overview of the security controls available on Azure Cosmos DB, refer to our security baseline.
Reviewing all past activity on their Cosmos DB accounts is also recommended to detect previous attempts to exploit this vulnerability.
While, at Microsoft’s request, the researchers have not yet released technical information regarding the ChaosDB flaw that could help threat actors create their own exploits, they will publish a full technical paper soon.
The Wiz research team has also recently disclosed a new class of DNS vulnerabilities impacting major DNS-as-a-Service (DNSaaS) providers that could enable attackers to access sensitive info from corporate networks in what was described as “nation-state level spying” campaigns.
Disclosure Timeline:
- August 09, 2021 – Wiz Research Team first exploited the bug and gained unauthorized access to Cosmos DB accounts.
- August 12, 2021 – Wiz Research Team sent the advisory to Microsoft.
- August 14, 2021 – Wiz Research Team observed that the vulnerable feature has been disabled.
- August 16, 2021 – MSRC confirmed the reported behavior (MSRC Case 66805).
- August 16, 2021 – Wiz Research Team observed that some obtained credentials had been revoked.
- August 17, 2021 – MSRC awarded a $40,000 bounty for the report.
- August 23, 2021 – MSRC confirms that several thousand customers are impacted.
- August 26, 2021 – Public disclosure.




