Microsoft Exchange servers now targeted by Black Kingdom ransomware

Another ransomware operation known as ‘Black Kingdom’ is exploiting the Microsoft Exchange Server ProxyLogon vulnerabilities to encrypt servers.
Over the weekend, security researcher Marcus Hutchins, aka MalwareTechBlog, tweeted that a threat actor was compromising Microsoft Exchange servers via the ProxyLogon vulnerabilities to deploy ransomware.
Based on the logs from his honeypots, Hutchins states that the threat actor used the vulnerability to execute a PowerShell script that downloads the ransomware executable from ‘yuuuuu44[.]com’ and then pushes it out to other computers on the network.
Honeypots are devices with known vulnerabilities exposed on the Internet to lure attackers and monitor their activities. Hutchins’ honeypots, though, did not appear to become encrypted, and the attack he witnessed was believed to be a failed campaign.
Someone just ran this script on all vulnerable Exchange servers via ProxyLogon vulnerability. It claims to be BlackKingdom “Ransomware”, but it doesn’t appear to encrypt files, just drops a ransom not to every directory. pic.twitter.com/POYlPYGjsz
— MalwareTech (@MalwareTechBlog) March 21, 2021
However, based on submissions to ransomware identification site ID Ransomware, the Black Kingdom campaign has encrypted other victim’s devices, with the first submissions seen on March 18th.
Michael Gillespie, the creator of ID Ransomware, told BleepingComputer that his system has seen over 30 unique submissions to his system, with many being submitted directly from mail servers.
Victims are located in the USA, Canada, Austria, Switzerland, Russia, France, Israel, United Kingdom, Italy, Germany, Greece, Australia, and Croatia.
When encrypting devices, the ransomware will encrypt files using random extensions and then create a ransom note named decrypt_file.TxT, as shown below. Hutchins states that he saw a different ransom note named ReadMe.txt that uses slightly different text.
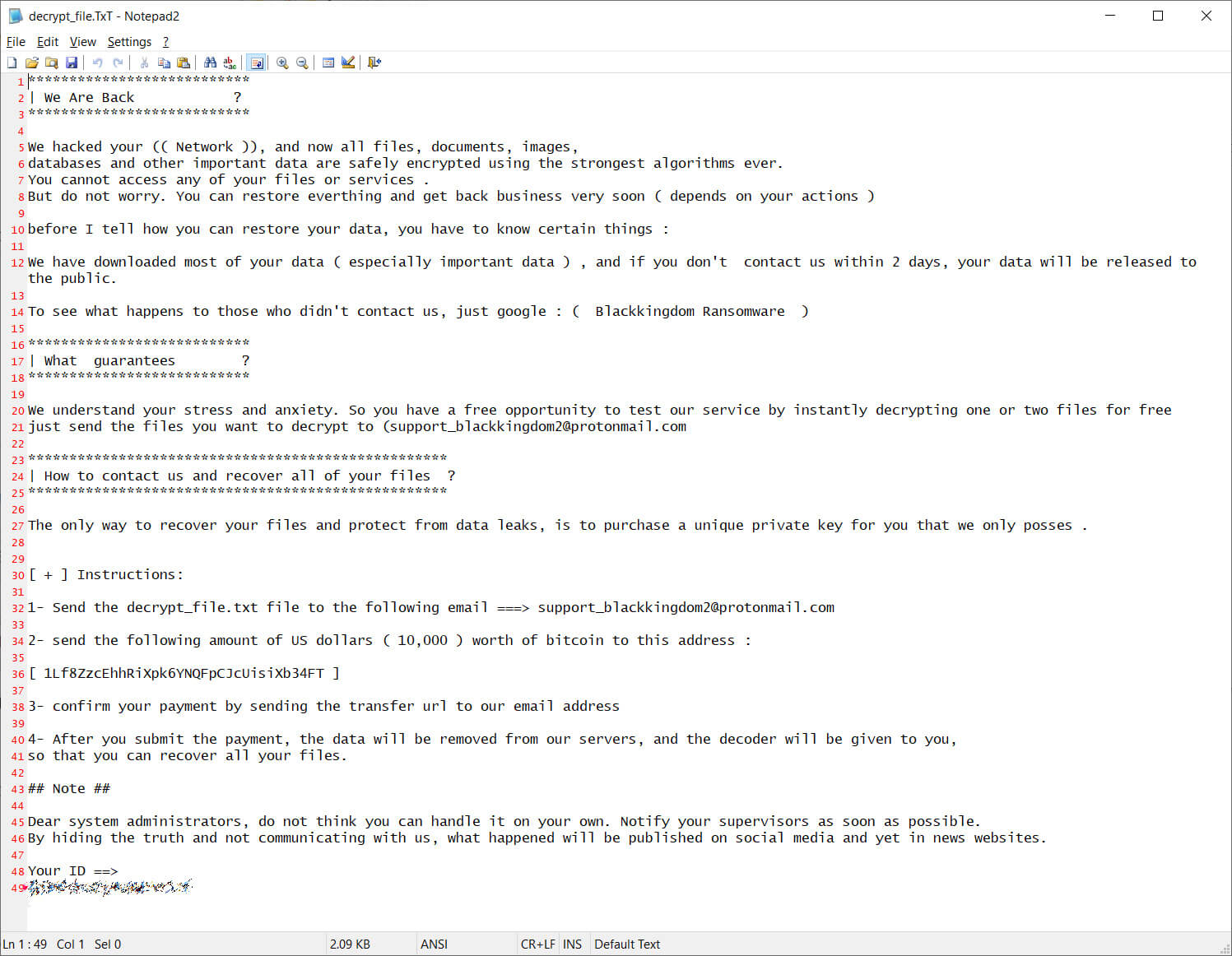
The ransom notes seen by BleepingComputer all demand $10,000 in bitcoin and use the same Bitcoin address (1Lf8ZzcEhhRiXpk6YNQFpCJcUisiXb34FT) for payment. This Bitcoin address has received only one payment on March 18th, which has since been transferred to another address.
Another ransomware known as BlackKingdom was previously used in attacks in June 2020 when corporate networks were compromised using Pulse VPN vulnerabilities.
While it has not been confirmed if the recent attacks and the ones from the summer of 2020 are using the same ransomware, Hutchins states that the current ransomware executable is a Python script compiled into a Windows executable. The Black Kingdom ransomware from June 2020 was also coded in Python.
If you are a victim of the recent Black Kingdom attacks, cybersecurity firm Emsisoft may be able to provide some help in recovering files.
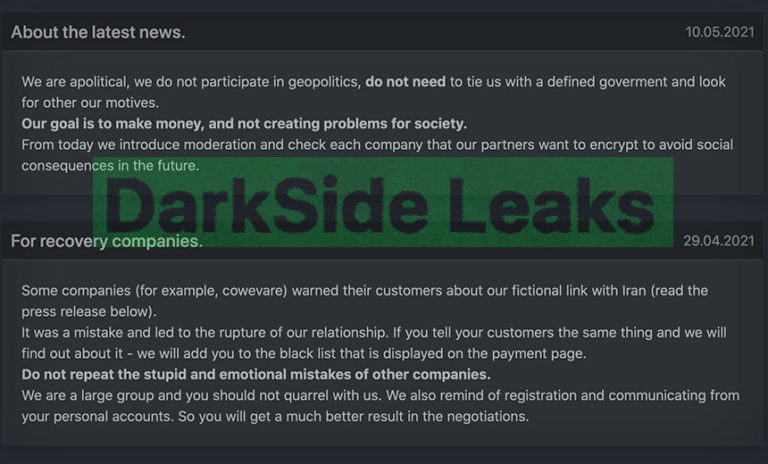
Black Kingdom is the second confirmed ransomware targeting the Microsoft Exchange ProxyLogon vulnerabilities. The first was the DearCry ransomware that was used in limited attacks earlier in the month.
Recently, leading electronics maker Acer also suffered a REvil ransomware attack that is suspected of having been conducted through ProxyLogon vulnerabilities. However, this has not been confirmed.