Is Darknet Forum Ransomware Chatter Ban Having an Impact?
Cybercrime
,
Fraud Management & Cybercrime
,
Fraud Risk Management
Report: XSS and Exploit Forum Members Using Workarounds to Violate the Ban
The decision by the Russian-speaking darknet forums XSS and Exploit to ban all chatter relating to ransomware attacks has had a limited impact on cyber gangs’ ability to communicate, according to the threat intelligence firm Digital Shadows.
See Also: Live Panel | How Organizations Should Think About Zero Trust
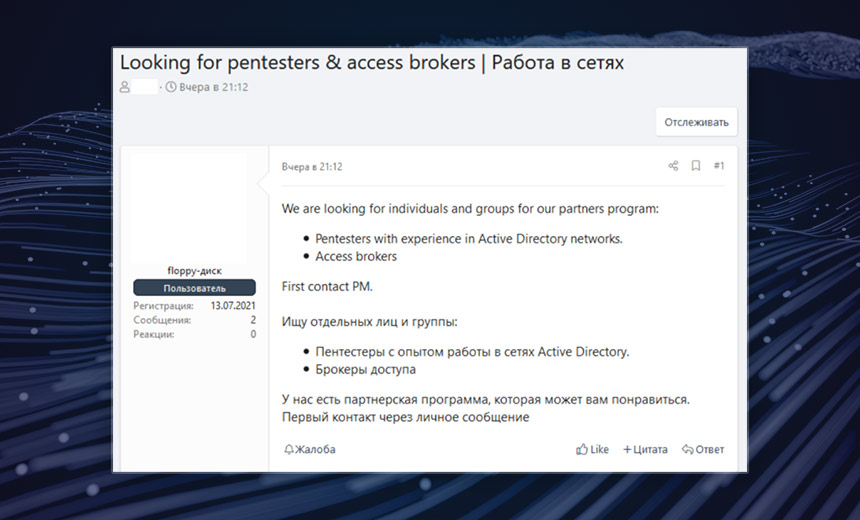
“Ransomware group representatives continue to regularly advertise vacancies for pentesting and privilege escalation specialists on forums and continue to update their data leak sites,” according t a new report from Digital Shadows’ Photon Research Team.
What Was Banned
In May, XSS and Exploit each banned any discussion related to ransomware and ransomware as a service. And the moderators deleted older conversations on the topic in an effort to avoid any confrontation with law enforcement agencies, Digital Shadows says. The operators hoped the ban would alleviate a focus on the forums by the federal government and law enforcement agencies as a result of the disruptive ransomware attack by DarkSide on Colonial Pipeline in June and REvil‘s attack on the remote management software company Kaseya.
DarkSide and REvil had representatives operating on each forum, the report notes.
DarkSide‘s attack on Colonial Pipeline temporarily disrupted fuel deliveries to much of the East Coast, while REvil’s attack affected 60 of Kaseya‘s managed service provider customers and up to 1,500 of their clients.
Once the two forums’ ransomware chatter ban was in place, accounts belonging to REvil and DarkSide were banned by XSS and Exploit. Soon after, accounts by the gang Avaddon also were banned, the report says.
Many of XSS and Exploit’s forum members applauded the ban on ransomware, calling the activity immoral, Digital Shadows says. But others took an opposing view.
“Many forum users had called for ransomware to be banned even before this ruling, particularly after a woman died in Germany after the hospital treating her fell victim to a ransomware attack in September 2020,” Digital Shadows says. “However, many other users reacted negatively, dismissing ‘the morality police’ and predicting that the forums would suffer without the revenue generated through the ransomware trade.”
Bending the Rules
Digital Shadows points out that many darknet forum members are not inclined to follow any rules, much less those imposed by a forum. This has proven true for XSS and Exploit, because the ban has led threat actors to try different methods of communication as a workaround, the threat intelligence firm reports.
“It seems that as long as ransomware representatives refrain from using the word ‘ransomware’ in their posts, they are allowed to stand,” Digital Shadows notes.
The forums’ moderators, however, are attempting to control what is said and have blocked certain users who have broken the rules, such as by discussing or advertising ransomware-as-a-service offerings, according to the threat intelligence firm’s report.
“While the trade in ransomware-related services has largely disappeared from the cybercriminal forums that implemented the ban, we have still seen threads discussing ransomware-related issues, such as what to do with system accesses previously destined for ransomware affiliates, speculation about potential law enforcement involvement in ransomware campaigns, cooperation between national law enforcement agencies in counter-ransomware operations and predictions about the future of ransomware,” the report notes.
In some cases, the forum operators are allowing smaller violations to continue, Digital Shadows says.
“This strict approach isn’t universal, though, and not all new ransomware-related posts are being flagged,” the report states. “For example, one forum member shared a link to the Himalaya RaaS recruitment page with no negative consequences. We have also seen users sharing Petya ransomware source code and advertising a Chaos ransomware builder, a Thanos ransomware builder and decryptor, and a GitHub submission for Ryuk ransomware.”
This could indicate that other forum members don’t bother reporting possible violations or the moderators don’t have the time and bandwidth to respond to all offending content.
Digital Shadows also says that, eventually, the forum operators will simply ignore their own regulations and allow ransomware conversations to resume. This is the case with numerous other “rules” on cybercriminal platforms, the analysts say.
Shifts to Other Forums
Meanwhile, Digital Shadows says that many ransomware attackers have shifted away from these two forums to use other sites.
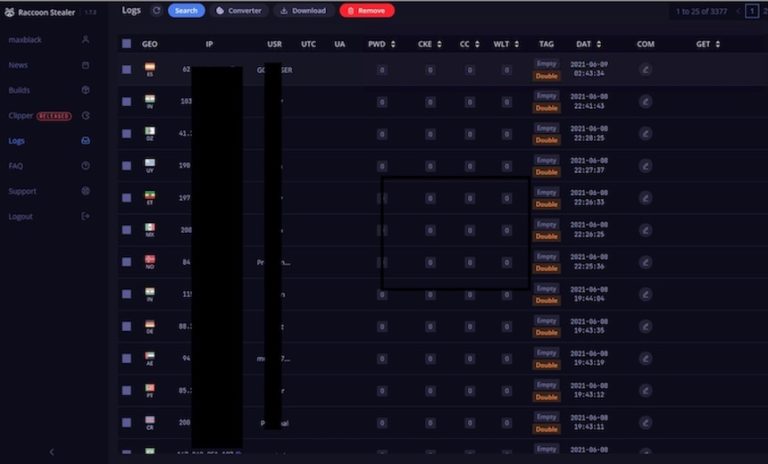
“Ransomware groups may also be using other platforms to recruit, e.g., private messaging applications,” the team says, pointing to the darknet forum RAMP as one such newly created criminal resource.