Howard University Hit With Ransomware Attack
Breach Notification
,
Critical Infrastructure Security
,
Cybercrime
Classes Canceled as the University’s IT Staff Repairs Damage

Stay tuned for updates on this developing story.
See Also: Top 50 Security Threats
Howard University canceled classes Tuesday in the wake of a ransomware attack it first detected on Friday, the institution announced. There is no evidence the attackers accessed or exfiltrated personal information, the school says.
The Washington, D.C.- based university’s IT team “detected unusual activity on the school’s network” and then followed its cyber response protocols in subsequently shutting down its network to investigate, Howard says.
The university is investigating the incident, but it has gathered enough information to say the malware involved was ransomware. The type of ransomware has not been revealed nor has any ransom amount demanded by the attacker. The institution says it’s working with external forensics experts and law enforcement authorities to assess the attack and has also contacted the FBI and the Washington, D.C., city government.
Officials at Howard University did not immediately respond to a request for more information associated with the incident, including technical details.
In an update Tuesday, Howard said remote and hybrid classes will remain canceled through Wednesday, while in-person courses will resume as scheduled.
With the start of a new semester and millions of students returning to college campuses around the country for the first time since the COVID-19-related shutdown in 2020, the threat actors likely believe that colleges will quickly pay the ransom because they want to minimize damages caused by a prolonged lockdown, says Sam Curry, chief security officer with Cybereason.
The university says its enterprise technology services team is working to restore operations as quickly as possible, but notes that “remediation, after an incident of this kind, is a long haul – not an overnight solution.”
The school adds: “We continue to work toward clarifying the facts surrounding what happened and what information has been accessed.”
Officials say campus Wi-Fi will remain down until the university “determines the best and safest path to stand it up.” In an update Tuesday, officials said they will be deploying an “alternative Wi-Fi system.” They note that cloud applications “remain active and accessible.”
Officials plan daily updates on the status of campus operations.
“We recognize that there has to be a balance between access and security; but at this point in time, the university’s response will be from a position of heightened security,” officials note.
Calling the situation “highly dynamic,” the officials say, “it is our priority to protect all sensitive personal, research and clinical data.” The university is also installing “additional safety measures to further protect … personal data from any criminal ciphering.”
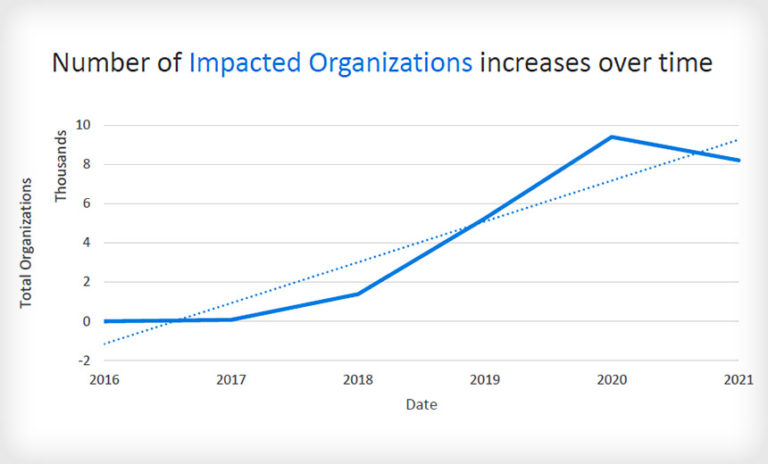
Targeted Attacks on the Rise
This cyberattack – targeting higher education – follows a string of incidents affecting other sectors this year – including Colonial Pipeline Co., Brazilian-based meat processor JBS and managed service provider Kaseya‘s remote management software platform.
Tim Erlin, vice president of strategy at the security firm Tripwire, says of these developments: “It’s easy to view the increase in ransomware headlines as a material change in the cybersecurity landscape, but it’s important to remember that ransomware has to announce itself to be successful.
“Universities are [particularly] tough environments to secure. They accept all kinds of devices into their networks and they change out their users at a high rate as students graduate and matriculate. Not many other IT organizations have to deal with all of these factors.”
Chris Clements, vice president of solutions architecture at the security firm Cerberus Sentinel, adds, “Educational institutions … are typically soft targets … and often university departments enjoy independence from each other that can lead to sprawling, disparate technology … that can remain unpatched or orphaned with no centralized oversight by IT.
“Ransomware gangs know that universities … can produce huge amounts of money to pay ransoms when forced to. This combination of relative ease of compromise and high ability to pay out extortion demands make universities incredibly lucrative targets for cybercriminals.”
News Editor Doug Olenick contributed to this report.