Fat Face’s ‘Strictly Private’ Data Breach Notification
Breach Notification
,
Incident & Breach Response
,
Security Operations
So Are We Supposed to Keep This Data Breach Notification Just Between Us Friends?
(See update on Fat Face paying a $2 million ransom.)
See Also: Live Webinar | Mitigating the Risks Associated with Remote Work
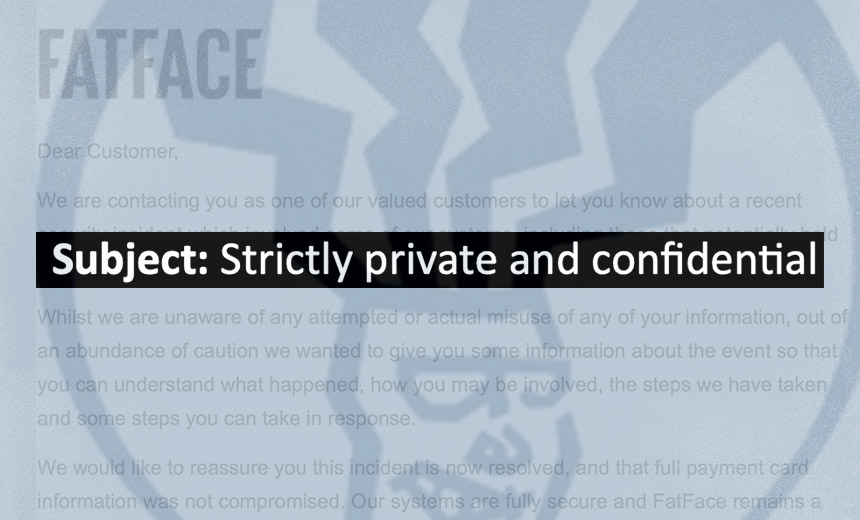
What happens when an e-commerce retailer sends you an email with a subject line that reads “strictly private and confidential – notice of security incident”?
“I’m so confused having read their email, is this data breach something serious that we should take immediate action on, or is it a minor breach?”
British clothing and accessories retailer Fat Face suffered a data breach affecting customer and employee data, as I first reported on Tuesday (see: British Clothing Retailer Fat Face Discloses Data Breach).
Now, if a letter arrives addressed to you marked “private and confidential,” it implies your secretary – should you have one – or anyone else shouldn’t open it. But in email land, it’s nonsensical. In fact, it reads like a company telling recipients: Don’t tell anyone, or you may face legal peril.
“Clearly trying to make people stay quiet,” one unamused Fat Face customer who shared the email with me said.
So for my news report, I contacted Britain’s Information Commissioner’s Office to ask if labeling a data breach notification “strictly private and confidential” was acceptable, since to me it looked like an inexpert attempt to try and hush up the incident. While the privacy watchdog, which enforces the General Data Protection Regulation in the U.K., told me it’s “making inquiries” about the breach, it declined to respond to that specific question.
Likewise, I queried Fat Face to ask about its choice of language, noting that it seemed odd because the breach is a public matter. What was it thinking?
A spokesman for the retailer told me: “The notification email was marked private and confidential due to the nature of the communication, which was intended for the individual concerned. Given its contents, we wanted to make this clear, which is why we marked it private and confidential.”
Clearly, this makes no sense. Emails that get emailed to an individual go to the individual. If you don’t want people to share the information, then ask nicely – but given that you lost control of people’s personal details, don’t expect victims to be happy.
And apparently, the notification language wasn’t used just to communicate with affected customers. TechCrunch reports that that affected employees received a similarly worded notification.

In terms of keeping the contents private, the email does contain information about how the affected customer can access 12 months of a prepaid identity theft monitoring service from Experian. To sign up, affected customers can phone a customer service line that will be open for just three weeks, which Fat Face says is the quickest way to make contact, or else email the company.
Presumably, Fat Face would prefer recipients not publish this information to prevent customers who haven’t received a breach notification from phoning just to make sure they weren’t affected too.
If Fat Face was smart, it might have anticipated this by setting up an in-house version of Have I Been Pwned, which would allow customers to enter their email address. Then Fat Face could email them directly to say whether their information appeared to have been compromised in this particular breach.
‘Should We Be Unduly Concerned?’
In the notification, Fat Face tells affected customers that attackers stole their names, email addresses, physical addresses and the last four digits of payment cards, together with expiration dates.
Fat Face says that the stolen “payment card information cannot be misused for fraudulent transactions, so you do not need to cancel your payment card on this basis,” and also that “no other financial data relating to you was involved in this incident.”
Despite the breach notification, many customers say they’re none the wiser about whether they’re somehow at increased risk.
“My wife received their email this morning. Should we be unduly concerned about identity theft?” one reader asked me on Wednesday.
Another customer said: “I’m so confused having read their email, is this data breach something serious that we should take immediate action on, or is it a minor breach? Especially unclear given they waited two months to mention it!”
Fat Face says it waited two months to notify victims, “to identify precisely what information was involved.” It declined to tell me precisely how many individual customers’ and employees’ data was exposed in the breach.
What’s the risk?
Speaking with security experts, the collective best guess is that, based on the exposed data, customers are at greatest risk of social engineering – for example, getting phoned by fraudsters who use the stolen information to try to extract additional details from victims, such as their full credit card numbers.
Individuals whose information was exposed could also be at risk of identity theft from scammers who attempted to apply for things in their name. The service being offered by Fat Face, for example, “helps detect possible misuse of your personal data including due to reasons beyond this incident and provides you with identity monitoring support, focused on the identification and resolution of identity theft.”
Language Matters
When organizations issue a data breach notification to customers or users, they’re already in the wrong. Having been trusted to safeguard private information, they failed to do so. Hence, a good starting point is to take every possible step to own the mistake. Doing anything that looks like you’re trying to hush it up is a no-no.
What about Fat Face taking two months to notify customers and possibly also employees?
“FatFace’s priority has been to clearly identify who was (and was not) involved in this incident and to identify precisely what information was involved, so that we could explain to you what happened and let you know what you can do in response,” the company says in its notification.
Data breach experts often recommend that breached organizations wait to directly notify victims – so long as victims are not at immediate risk and regulations do not require otherwise – until they can tell them precisely what happened and what they can do about it. This helps avoid “breach fatigue.” (See: Data Breach Notifications: What’s Optimal Timing?)
Having investigated the breach, Fat Face now seems to know who was affected, and thus is directly telling victims – albeit via some dubious language – that it’s bought them 12 months of prepaid identity theft monitoring, if they want it, and that they should be extra aware of any attempts to scam them.

Breach Notification Bingo
Breached organizations often use a litany of tricks to imply that they were the victim of circumstances beyond their control (see: Blackbaud’s Bizarre Ransomware Attack Notification).
To be clear, no breached business – at least that I’m aware of – has yet claimed to have been hacked by ninja cyberwarriors from Mars. (Malicious insiders are from Venus.) But too many organizations, including Fat Face, unleash various hedges and rhetorical blame-shifting tricks. Those include:
- Minimizing the risk to victims: Organizations that have not yet been presented with direct evidence that the data attackers stole has been used to commit identity theft or fraud often claim they’re providing fraud protection services simply out of an “abundance of caution.”
- Making hacking look normal: Like death and taxes, Fat Face suggests falling victim to criminal hackers is inevitable. “Unfortunately, like many organizations, we were subject to a sophisticated criminal attack which involved access to our systems,” it says.
- Blame the hacker ninjas: Attackers are never script-kiddie lazybones who were able to pop the company using an automated tool and relatively scant technology skills. Inevitably, they must have been “sophisticated.”
- Proclaiming you care: “Fat Face takes the security of your information extremely seriously,” says the organization that just failed to protect it.
- Police alerted: Too late for it to have prevented the breach, hacked organizations love to tell everyone that they’ve “notified law enforcement authorities of this incident.”
- Profound use of passive voice: Few say: “We failed to stop hackers from stealing your data.” Instead, the passive voice predominates. “We were subject to a sophisticated criminal attack,” Fat Face says. Then its customers were arguably subjected to its breach notification.
What would be truly “sophisticated” is clear evidence of an organization having maintained a top-notch security program. Of course, sometimes attackers get through anyway. At which point, wouldn’t it be great if the breached business simply told customers in a clear manner precisely what happened, including any of its own failures, and clearly set out the potential risks customers now face?