CVE-2021-34392
Trusty TLK contains a vulnerability in the NVIDIA TLK kernel where an integer overflow in the tz_map_shared_mem function can bypass boundary checks, which might lead to denial of service.

The latest edition of the ISMG Security Report features an analysis of data breach trends as well as other updates. In this report, you’ll hear (click on player beneath image to listen): ISMG’s Mathew Schwartz describe how phishing, ransomware and unauthorized access remain the leading causes of personal data breaches in Britain; …
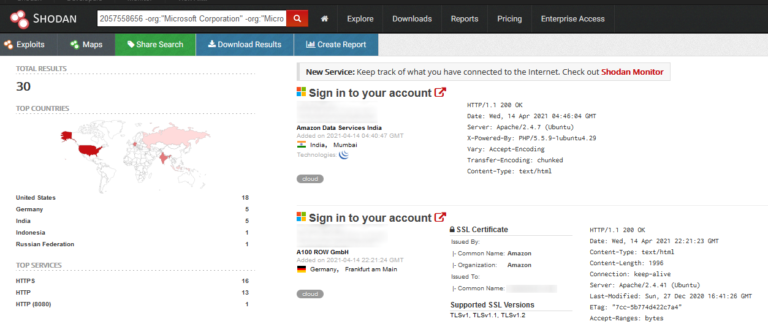
HTTP favicons are often used by bug bounty hunters and red teamers to discover vulnerable services in a target AS or IP range. It makes sense since different tools (and sometimes even different versions of the same tool) use different favicons[ 1 ] and services such as Shodan calculate MurmurHash….

Cisco Systems has agreed to purchase Kenna Security to help customers more effectively prioritise vulnerabilities based on threat intelligence and business impact. The San Jose, Calif.-based networking giant said its proposed acquisition of Santa Clara, Calif.-based Kenna will make it easier for organizations to work cross-functionally to rapidly identify, prioritize and remediate cyber risk. This…

Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Agency Now Seeks Feedback to Help Address Governance Challenges Dan Gunderman (dangun127) • July 31, 2021 (Photo: Gerd Altmann/Pixabay) Citing a need to secure artificial intelligence technologies, the National Institute of Standards and Technology is working to…
Amid heightened border tensions between India and China, cybersecurity researchers have revealed a concerted campaign against India’s critical infrastructure, including the nation’s power grid, from Chinese state-sponsored groups. The attacks, which coincided with the standoff between the two nations in May 2020, targeted a total of 12 organizations, 10 of which are in the power…

Softpedia News / Security 5. May 2021 Multiple critical vulnerabilities have been discovered in the Exim email server software by the Qualys Research Team. Some of these flaws can be chained together to achieve full remote unauthenticated code execution and root privileges. Exim is a widely used mail transfer agent (MTA) that even comes pre-installed…