Critical RCE Vulnerability Found in VMware vCenter Server — Patch Now!
VMware has rolled out patches to address a critical security vulnerability in vCenter Server that could be leveraged by an adversary to execute arbitrary code on the server.
Tracked as CVE-2021-21985 (CVSS score 9.8), the issue stems from a lack of input validation in the Virtual SAN (vSAN) Health Check plug-in, which is enabled by default in the vCenter Server. “A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server,” VMware said in its advisory.
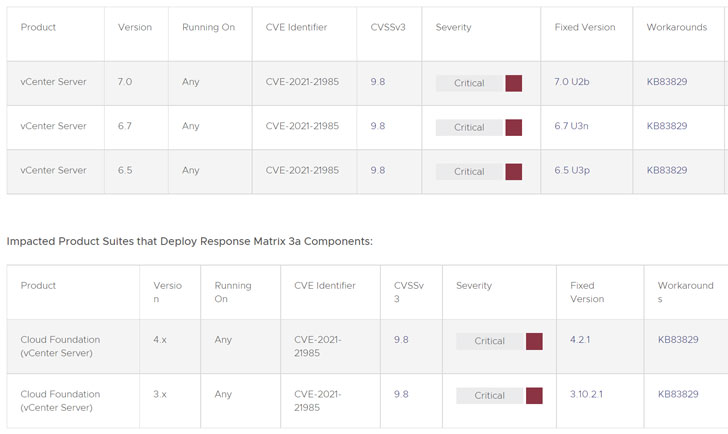
VMware vCenter Server is a server management utility that’s used to control virtual machines, ESXi hosts, and other dependent components from a single centralized location. The flaw affects vCenter Server versions 6.5, 6.7, and 7.0 and Cloud Foundation versions 3.x and 4.x. VMware credited Ricter Z of 360 Noah Lab for reporting the vulnerability.
The patch release also rectifies an authentication issue in the vSphere Client that affects Virtual SAN Health Check, Site Recovery, vSphere Lifecycle Manager, and VMware Cloud Director Availability plug-ins (CVE-2021-21986, CVSS score: 6.5), thereby allowing an attacker to carry out actions permitted by the plug-ins without any authentication.
While VMware is strongly recommending customers to apply the “emergency change,” the company has published a workaround to set the plug-ins as incompatible. “Disablement of these plug-ins will result in a loss of management and monitoring capabilities provided by the plug-ins,” the company noted.
“Organizations who have placed their vCenter Servers on networks that are directly accessible from the Internet […] should audit their systems for compromise,” VMware added. “They should also take steps to implement more perimeter security controls (firewalls, ACLs, etc.) on the management interfaces of their infrastructure.”
CVE-2021-21985 is the second critical vulnerability that VMware has rectified in the vCenter Server. Earlier this February, it resolved a remote code execution vulnerability in a vCenter Server plug-in (CVE-2021-21972) that could be abused to run commands with unrestricted privileges on the underlying operating system hosting the server.
The fixes for the vCenter flaws also come after the company patched another critical remote code execution bug in VMware vRealize Business for Cloud (CVE-2021-21984, CVSS score: 9.8) due to an unauthorized endpoint that could be exploited by a malicious actor with network access to run arbitrary code on the appliance.
Previously, VMware had rolled out updates to remediate multiple flaws in VMware Carbon Black Cloud Workload and vRealize Operations Manager solutions.