Botnet Data Leak: 26 Million Passwords Exposed
Cybercrime
,
Data Loss Prevention (DLP)
,
Endpoint Security
1.5 Million Facebook Passwords Among Leaked Data; Raccoon Infostealer Suspected
There’s such a surfeit of stolen data floating around on dark web forums that it’s overwhelming. Passwords and other credentials collected are bought and sold on an industrial scale.
See Also: Live Webinar: Seeking Success by Adopting a SASE Architecture: en el idioma Español
On Wednesday, a 1.2 terabyte batch of data was highlighted by NordLocker, which is part of the Nord family of security products. In a blog post, NordLocker says the data, which was for sale, was accidentally revealed by a hacking group. It was hosted on a cloud service, which was then notified, and the data was taken down.
Although this data isn’t unique in either quantity or how it was collected, it could help with enterprise-level exploitation, including fraud, ransomware and other schemes.
On its own, this is workaday botnet data: credential pairs dumped from browsers, files pinched from desktop and download folders, and cookies snatched from browsers.
It’s the kind of material that routinely shows up on the dark web, both for sale and, sometimes, for free, says Alex Holden, CISO of Hold Security, a Wisconsin-based security consultancy. Holden says his company recovered 6.8TB of botnet data alone last week, which is a routine figure.

But what NordLocker discusses does show a hostile malware landscape that can result in the loss of sensitive data. And although this data isn’t unique in either quantity or how it was collected, it could help with enterprise-level exploitation, including fraud, ransomware and other schemes.
“There is an entire underground economy based on botnet data,” Holden says.
For example, Colonial Pipeline Co.’s ransomware incident occurred due to reuse of credentials for an old VPN account that should have been deactivated. Those VPN credentials were found in a data breach, although it is unknown if that’s how the attackers obtained the credentials. It has been suggested that a Colonial employee might have reused those credentials on another service, which was then breached (see: Colonial Attackers Used Compromised VPN Credentials).
Compromised: 26 Million Login Credentials
The data found by NordLocker was collected from 3.25 million Windows computers between 2018 and last year. All told, there were 26 million sets of login credentials from 1 million websites, NordLocker says.
Included are 1.5 million Facebook passwords and nearly 20 million other credentials stored by users in Google’s Chrome browser. Also nicked were 2 billion cookies, or data files that store user preferences and allow people to remain logged into a website. NordLocker says that 22% of the cookies – which included those for services such as YouTube, AliExpress, LinkedIn and Steam – were still valid when it found the data.
The malware also stole around 6 million files, including 1 million images and 650,000 Word documents and PDF files. Once the malware landed on a machine with a webcam, it took a photo, potentially capturing whomever was using the computer at the time.
It’s not clear what type of malware infected the computers, but NordLocker says that screenshots revealed that it had spread via pirated versions of such software as Adobe Photoshop, games and Windows cracking tools. We’ve all been warned for years about downloading “free” software, so that might say something about the types of people infected with this botnet code.
Holden says based on the data collected, an “infostealer” known as Raccoon could be a likely suspect. Other well-known infostealer botnets include AzorUlt and Vidar, which also flood black markets with credentials and data in huge quantities, he says.
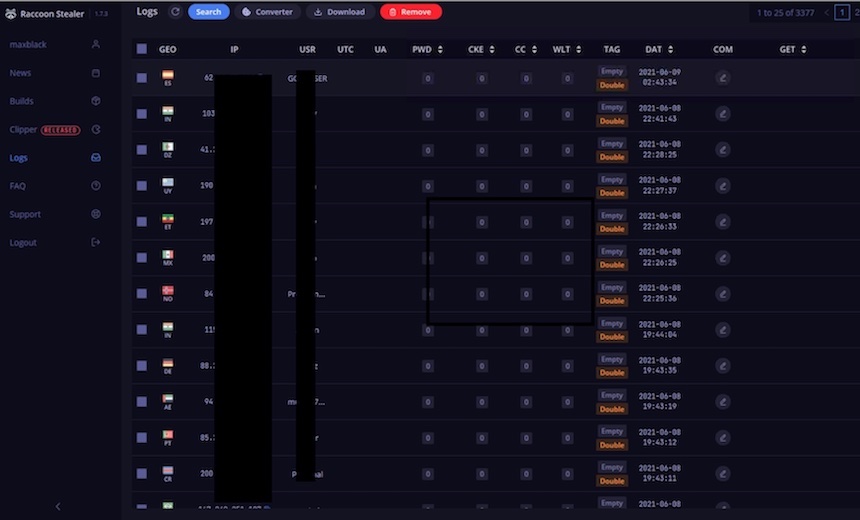
Raccoon is malware as a service, and subscribers can pick and choose infected machines from a control panel that runs as a Tor hidden service to see what data the botnet has collected from victims. Batches of Raccoon data frequently leak.
“We have seen Raccoon data dumps everywhere, and they are huge in size,” Holden says. “Unfortunately the truth is there are so many victims. There’s an immeasurable amount of data that I see being laundered every day.”
Are You Affected?
The difference with this incident is there is a chance that some of those affected will be notified.

Troy Hunt, who runs the free Have I Been Pwned data breach notification service, has added this breach to HIBP. Hunt says in a blog post that there are 1.1 million unique email addresses in the data
Hunt tells me that for this breach, HIBP has sent out around 1,000 notifications to individuals and about 4,000 notifications to organizations monitoring their domains. Over the years, Hunt has increasingly added to HIBP breaches that do not have a clear source, such as spam lists and credential stuff lists.
That offers at least a chance of helping people be aware of such data being exposed. Then they can hopefully take defensive steps, such as changing their passwords to stronger ones and removing malware from their computer.
Oh, and one last piece of advice: Break the habit of downloading software bundled with an infostealer.





