Attackers Increasingly Using Cobalt Strike
Cybercrime
,
Fraud Management & Cybercrime
,
Fraud Risk Management
Report: Pen Testing Tool a Favorite Among Lower-Level Threat Groups
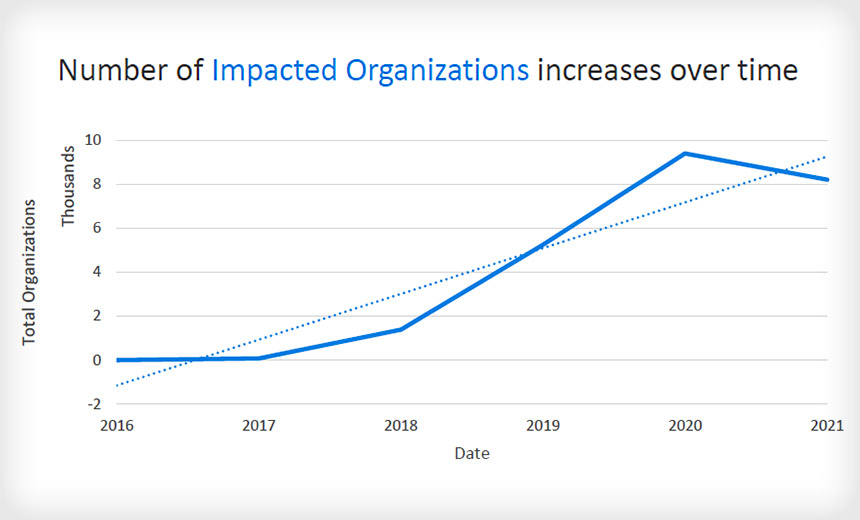
The legitimate security penetration testing tool Cobalt Strike is increasingly being used by threat groups, especially those that are less technically proficient, according to a Proofpoint report released Tuesday.
See Also: Live Panel | Zero Trusts Given- Harnessing the Value of the Strategy
Researchers at the security firm say the number of attacks using Cobalt Strike increased 161% between 2019 and 2020, and the tool remains a high-volume threat in 2021. It’s been used in a wide variety of attacks – including the SolarWinds supply chain attack – and for cyberespionage campaigns, leading Proofpoint to conclude that it’s a favorite tool of advanced persistence threat groups.
“Cobalt Strike is used by a diverse array of threat actors, and while it is not unusual for cybercriminal and APT actors to leverage similar tooling in their campaigns, Cobalt Strike is unique in that its built-in capabilities enable it to be quickly deployed and operationalized regardless of actor sophistication or access to human or financial resources,” Proofpoint says.
Why Attackers Like Cobalt Strike
Some of the tool’s useful features for an attacker are its user-friendliness, its obfuscation capabilities and its ability to be used as either a first- or second-stage downloader. Proofpoint notes that as Cobalt Strike has been updated over the years, it has moved from being used almost exclusively by well-resourced crime groups – such as FIN7, the APT group Leviathan and APT40 – to becoming more mainstream for a broader range of criminals.
One reason for that is that Cobalt Strike is easy to obtain. An attacker can attempt to buy it legitimately from the developer, although there’s a verification process in place to ensure the tool does not fall into the hands of a cybercriminal. And the tool is also widely available for purchase on the darknet, including a cracked version of the latest Cobalt Strike 4.0, Proofpoint says.
The software is highly customizable and can be removed without leaving any evidence behind. It can help enable an attacker to exfiltrate data, drop a second payload and essentially behave as if it belongs inside a system.
“Cobalt Strike is also session-based – that is, if threat actors can access a host and complete an operation without needing to establish ongoing persistence, there will not be remaining artifacts on the host after it is no longer running in-memory. In essence: They can hit it and forget it,” Proofpoint says.
HelpSystems, which developed Cobalt Strike, did not immediately reply to a request for comment on the Proofpoint report.
Groups Using Cobalt Strike as Malware
“Threat actors can also use the malleability of Cobalt Strike to create customized builds that add or remove features to achieve objectives or evade detection,” according to Proofpoint. “For example, APT29 frequently uses custom Cobalt Strike Beacon loaders to blend in with legitimate traffic or evade analysis,” the security firm says.
Another group known to use Cobalt Strike is the crime gang TA800, which specializes in banking malware attacks. TA800 recently underwent a shift in how it delivers Cobalt Strike. Starting in 2019, after gaining initial entry, the gang would inject BazaLoader, which downloads Cobalt Strike. In February, the group reversed this process, distributing Cobalt Strike as a first-stage payload via malicious URLs.
Also in February, TA547, which uses banking Trojans, began distributing Cobalt Strike as a second-stage payload to establish command and control, Proofpoint says.
Barium, also known as APT41 and TA415, used Cobalt Strike in several campaigns in 2020. This group is believed to be associated with the People’s Republic of China’s Ministry of State Security, Proofpoint says.
Cobalt Strike and SolarWinds
The group behind the SolarWinds supply chain attack, which the U.S. government believes to be Russian and which Microsoft named Nobelium, extensively used Cobalt Strike. A Microsoft analysis of the attack released in January showed the attackers used Cobalt Strike to maintain persistence and remain hidden to give them time to fully penetrate systems, move laterally through networks and exfiltrate data in follow-on attacks.
When activating the second stage of an attack, Microsoft said, the hackers “went out of their way” to ensure that the backdoor they initially installed in the SolarWinds’ Orion network monitoring platform was separated “as much as possible” from Cobalt Strike loader implants they used to escalate the attack, paving the way for exfiltrating data.
Microsoft says the attackers apparently believed that this approach meant that if Cobalt Strike – a legitimate penetration testing tool – was detected in an infected system, the victim would not notice the connection to the SolarWinds Orion backdoor.
Defending Against Cobalt Strike
Sherrod DeGrippo, senior director of threat research and detection with Proofpoint, says organizations can take steps to spot an illegitimate use of Cobalt Strike.
Email security tools can block first-stage delivery of Cobalt Strike, and threat detection tools can identify a generic instance of Cobalt Strike in a company network that is not associated with another legitimate process, she says.
“Defenders can look at network communications to identify unusual activity, disallow communications to unrecognized IP addresses or domains, etc. It can be difficult to detect/defend against the tool, however, there are multiple resources available for defenders,” DeGrippo says.
Other Legitimate Tools Being Used for No Good
Proofpoint’s researchers note that malicious actors are using other legitimate red team tools – including Mythic, Meterpreter and the Veil Framework – to ply their trade.
“Threat actors are using as many legitimate tools as possible, including executing Windows processes like PowerShell and WMI, injecting malicious code into legitimate binaries and frequently using allowable services, like Dropbox, Google Drive, SendGrid, and Constant Contact, to host and distribute malware,” Proofpoint says.