CVE-2021-22349
There is an Input Verification Vulnerability in Huawei Smartphone. Successful exploitation of insufficient input verification may cause the system to restart.

Today’s VERT Alert addresses Microsoft’s August 2021 Security Updates. VERT is actively working on coverage for these vulnerabilities and expects to ship ASPL-959 on Wednesday, August 11th. In-The-Wild & Disclosed CVEs CVE-2021-36948 This privilege escalation vulnerability that affects the Windows Update Medic Service (WaasMedic) has been actively exploited. Medic Service is a feature of modern…
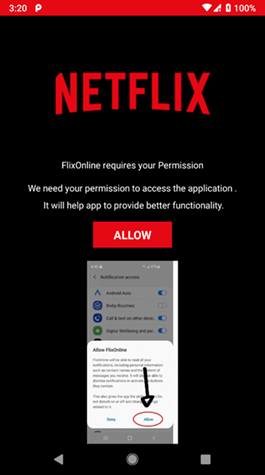
Researchers Flag ‘FlixOnline’ as a Malicious Android Play Store App That Combines Social Engineering With WhatsApp Auto-Replies to Propagate Researchers have discovered new Android malware that uses Netflix as its lure and spreads malware via auto-replies to received WhatsApp messages. The discovery was reported to Google, and the malware – dubbed FlixOnline – has been removed from…

Zerodium Will Triple Payouts for RCE Exploits for WordPress CMS – IT Security News 12. April 2021 Zerodium is an American security company, whose main business is to develop and acquire premium zero-day exploits from security researchers and report the research, along with protective measures and security recommendations, to its government…

Microsoft today announced plans to launch Windows 11 on October 5th, inviting us to a world of exciting new features like rounded corners and a new default desktop wallpaper. As new named versions of Windows goes, 11 seems a smaller upgrade than from, say, Windows 3.1 to Windows 95, or from Window 8 to straight-up…

Business Continuity Management / Disaster Recovery , Fraud Management & Cybercrime , Governance & Risk Management Director of HSE, Nation’s Healthcare System, Describes the Costs Akshaya Asokan (asokan_akshaya) • June 24, 2021 The recovery costs for the May ransomware attack on Health Service Executive, Ireland’s publicly funded healthcare system, is likely to total…

Cyber attack hits State Department in ‘possible serious breach’ Tap here to add The Western Journal to your home screen.