New Kubernetes malware backdoors clusters via Windows containers

New malware active for more than a year is compromising Windows containers to compromise Kubernetes clusters with the end goal of backdooring them and paving the way for attackers to abuse them in other malicious activities.
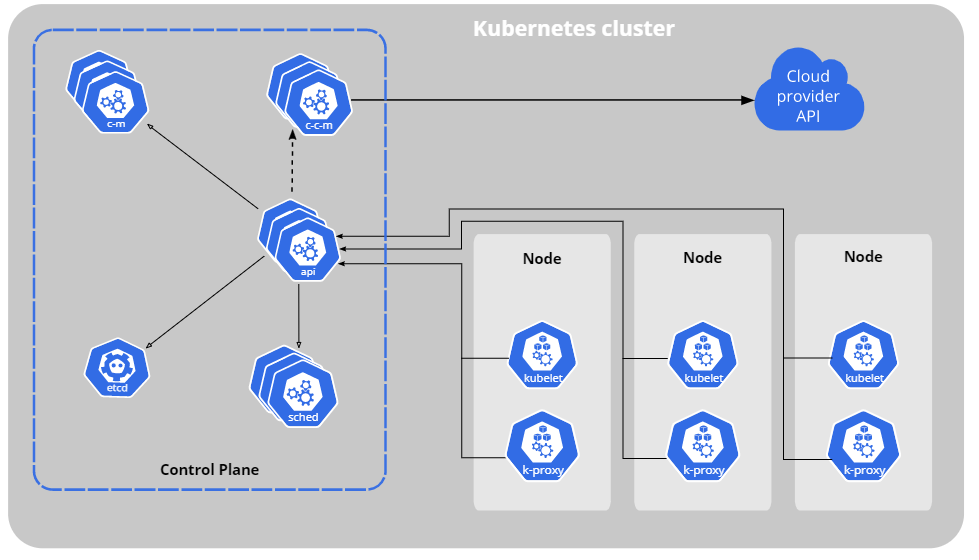
Kubernetes, initially developed by Google and currently maintained by the Cloud Native Computing Foundation, is an open-source system that helps automate the deployment, scaling, and management of containerized workloads, services, and apps over clusters of hosts.
It organizes app containers into pods, nodes (physical or virtual machines), and clusters, with multiple nodes forming clusters managed by a master which coordinates cluster-related tasks such as scaling or updating apps.
Ongoing attacks target Kubernetes clusters
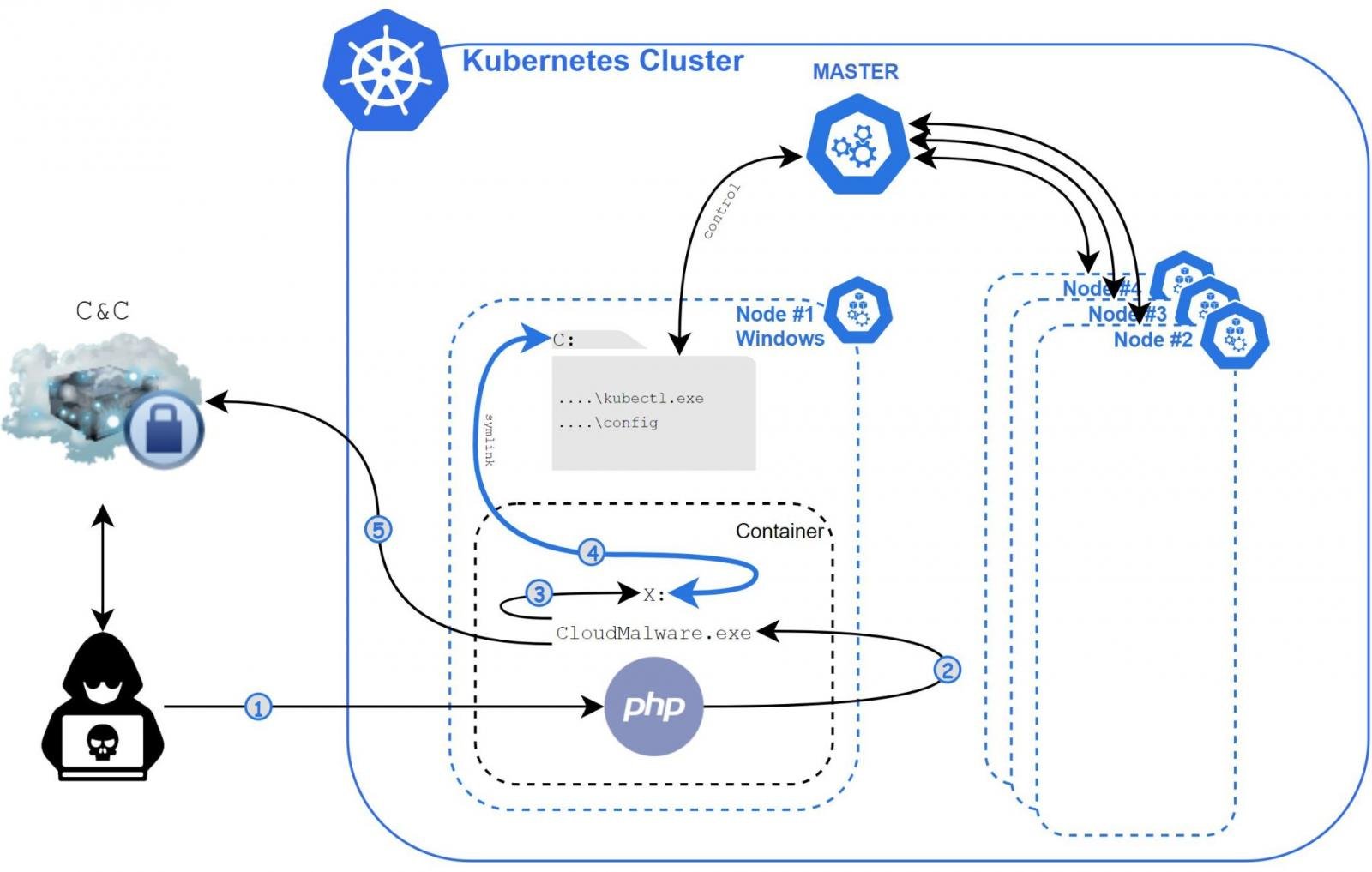
The malware, dubbed Siloscape by Unit 42 security researcher Daniel Prizmant and the first one to target Windows containers, exploits known vulnerabilities impacting web servers and databases with the end goal of compromised Kubernetes nodes and backdooring clusters.
“Siloscape is heavily obfuscated malware targeting Kubernetes clusters through Windows containers. Its main purpose is to open a backdoor into poorly configured Kubernetes clusters in order to run malicious containers,” Prizmant said in a report published today.
“Unit 42 researchers have previously only seen malware targeting containers in Linux due to the popularity of that operating system in cloud environments,” Unit 42 researchers Ariel Zelivansky and Matthew Chiodi added in a separate blog post.
Once it compromises the web servers, Siloscape uses various container escape tactics to achieve code execution on the underlying Kubernetes node.
Compromised nodes are then probed for credentials that allow the malware to spread to other nodes in the Kubernetes cluster.
In the final stage of the infection, the Siloscape malware establishes communication channels with its command-and-control (C2) server via IRC over the Tor anonymous communication network and listens for incoming commands from its masters.
After gaining access to the malware’s C2 server, Prizmant was able to identify 23 active victims and found that the server was hosting 313 users in total, hinting at Siloscape being just a tiny part of a much larger campaign.
“Investigating the C2 server showed that this malware is just a small part of a larger network and that this campaign has been taking place for over a year,” Prizmant added.
“Furthermore, I confirmed that this specific part of the campaign was online with active victims at the time of writing.”
Exposes victims to ransomware, supply-chain attacks
While most malware targeting cloud environments are focused on cryptojacking (secretly mining for cryptocurrency on infected devices) and abusing the infected systems for launching DDoS attacks, Siloscape is an entirely different beast.
First of all, it does its best to evade detection by avoiding any actions that could alert the compromised clusters’ owners to the attack, including cryptojacking.
Its goal is to backdoor the Kubernetes clusters, which opens the way for its operators to abuse the compromised cloud infrastructure for a broader range of malicious pursuits, including credential theft, data exfiltration, ransomware attacks, and even highly disastrous supply chain attacks.
“Compromising an entire cluster is much more severe than compromising an individual container, as a cluster could run multiple cloud applications whereas an individual container usually runs a single cloud application,” Prizmant concluded.
Kubernetes admins are advised to switch from Windows containers to Hyper-V containers and ensure that their cluster is securely configured to prevent malware like Siloscape from deploying new malicious containers.
Indicators of compromise (IOCs) and further technical details on the Siloscape malware are available in Prizmant’s report.