7 Emerging Ransomware Groups Practicing Double Extortion
Cybercrime as-a-service
,
Fraud Management & Cybercrime
,
Malware as-a-Service
Fresh Ransomware-as-a-Service Operations Seek Affiliates for Extorting New Victims

After a string of high-profile hits in the middle of this year, a number of the largest and most notorious ransomware operations disappeared.
See Also: Top 50 Security Threats
Beginning in May, ransomware attacks by Russian-language groups Conti against Ireland’s health service, DarkSide against U.S.-based Colonial Pipeline, and REvil against meat processing giant JBS and remote management software firm Kaseya led the Biden administration to try to better disrupt the ransomware business model. The White House has put Russia on notice that if it won’t disrupt ransomware-wielding criminals operating from inside its borders, then the U.S. reserves the right to do so.
In short order, DarkSide and REvil disappeared, as did Avaddon, with experts saying they appeared to be running scared. All were ransomware-as-a-service operations, in which operators develop crypto-locking ransomware and provide it to affiliates – essentially, self-employed contractors – who infect victims. Whenever a victim pays, the affiliate and operator share a prearranged split of the payoff.
Or at least that is what happens in theory. Security firm Recorded Future’s new site, The Record, recently reported that a disgruntled Conti affiliate leaked manuals and technical guides used to train affiliates, arguing that he’d been getting underpaid.
New and Rebranded Operations Emerge
Given the massive profit-making potential ransomware still offers, aided by many organizations being under-defended, many security experts believe that the core operators behind Avaddon, DarkSide and REvil will simply set up shop under a different name. Affiliates, meanwhile, often work with multiple ransomware operations, sometimes simultaneously. Hence, while some groups may appear to come and go, the ransomware business model surges on.
As always, new ransomware gangs regularly debut. In recent weeks, law enforcement officials and information security experts have been tracking a surge in activity from lesser-known players, including the emergence of new operations. All use double extortion, meaning they claim to steal data before crypto-locking systems, and threaten to leak the stolen data to a data-leak site unless victims pay.
Here are more details on seven such operations: ALTDOS, AvosLocker, Hive, HelloKitty, LockBit 2.0 and OnePercent Group, as well as the DarkSide spinoff BlackMatter.
1. ALTDOS
This week, Singapore’s Cyber Security Agency, police force and Personal Data Protection Commission warned that the ALTDOS cybercrime operation, since appearing last December, has continued to target organizations in Bangladesh, Singapore and Thailand.
“It is currently unknown which ransomware variant is employed by ALTDOS,” according to their joint advisory on ALTDOS. “ALTDOS will … contact the victim using an email address hosted on ProtonMail demanding that payment be made or the exfiltrated data will be published.”
The advisory adds: “If the victim does not respond or comply to the ransom demand within the given time frame, ALTDOS may also launch a distributed denial-of-service attack on the victim’s internet-facing systems to disrupt operational services and to remind them to pay the ransom.”
As with the aforementioned ransom groups, ALTDOS practices double extortion, meaning it shakes down victims to pay a ransom not just for a promise that they’ll receive in turn a decryption tool, but also for a promise that data stolen by attackers – before they crypto-locked systems – will get deleted. The advisory notes that the group sometimes demands separate ransom payments for a decryptor, versus a promise to delete stolen data.
2. AvosLocker
This operation was first spotted in June, with researchers saying it appeared to be focusing on smaller law firms, as well as freight, logistics and real estate firms, in the U.S., the U.K. and parts of Europe. But by the end of last month, the small operation appeared to still be trying to recruit more affiliates, for example, via spam advertisements distributed via Jabber and Telegraph.
“I am not sure there has been much uptake there,” Allan Liska, an intelligence analyst with Recorded Future’s computer security incident response team, said at the time. “They are definitely worth continuing to monitor.”
As of Thursday, AvosLocker’s Tor-based data-leak site listed 11 victims, including Moorfields Eye Hospitals UAE, which is a branch of the British National Health Service’s Moorfields Eye Hospital Foundation Trust, from which the group says it stole more than 60GB of data. Moorfields has confirmed the attack, though not attributed it.
“Like many of its competitors, AvosLocker offers technical support to help victims recover after they’ve been attacked with encryption software that the group claims is ‘fail-proof,’ has low detection rates and is capable of handling large files,” say Doel Santos and Ruchna Nigam of Palo Alto’s Unit 42 threat research group in a blog post. “We have observed initial ransom demands ranging from $50,000 to $75,000.”
3. Hive Ransomware

Experts say newcomer Hive ransomware, first spotted on June 26 by the self-described South Korea-based “ransomware hunter” behind the @fbgwls245 Twitter account, who spotted the group’s malicious executable after it was uploaded to the VirusTotal malware-scanning service.
On Thursday, Hive’s data-leak site listed 34 victims. “Hive uses all tools available in the extortion toolset to create pressure on the victim, including the date of initial compromise, countdown, the date the leak was actually disclosed on their site, and even the option to share the disclosed leak on social media,” Palo Alto’s Santos and Nigam say.
While the group may have already honed its shakedown tactics, however, the research and intelligence team at BlackBerry recently said that, based on observed samples of Hive, the malware appears to be very much “still under development.”
Lambasting the poor quality of the code, Brett Callow, a threat analyst at security firm Emsisoft, has told ISMG that that samples of Hive seen so far were using “an idiotic and amateurish cryptographic scheme in which 100 RSA keys of varying bit size are used to encrypt files,” which promised to complicate recovery.
4. HelloKitty
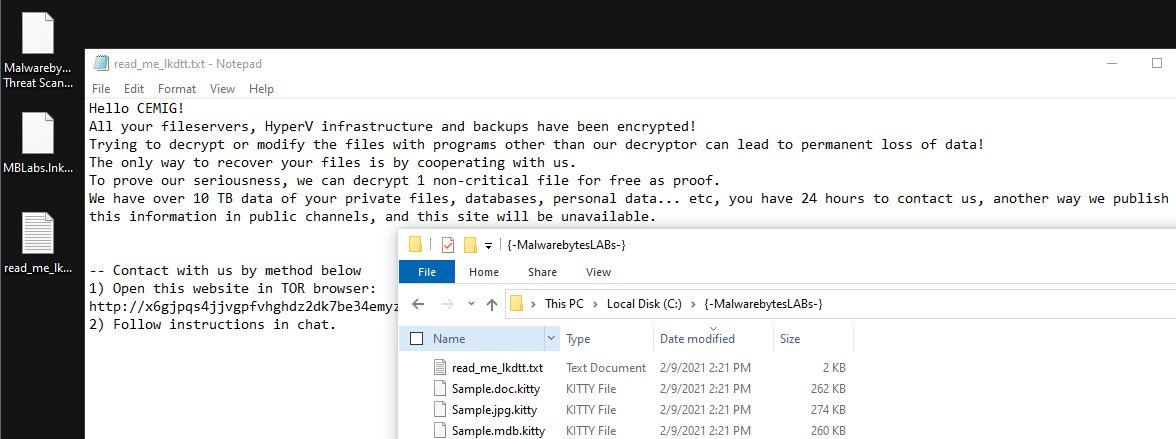
Attacks involving HelloKitty ransomware were first spotted in early 2020. In April, FireEye warned that attackers wielding HelloKitty had been targeting unpatched SonicWall SMA 100 Series unified access gateways. A zero-day flaw in the devices, designated CVE-2021-20016, was confirmed by the vendor on Jan. 23 and patched on Feb. 23.
In July, the Palo Alto researchers say they spotted “a Linux variant of HelloKitty targeting VMware’s ESXi hypervisor, which is widely used in cloud and on-premises data centers.” The ESXi hypervisor likely was being targeted because of the large ransoms that could be demanded if attackers successfully crypto-locked these systems. Palo Alto says that HelloKitty-wielding attackers have demanded ransoms of up to $10 million, but they recently received a trio of large ransoms that added up to just $1.5 million.
5. LockBit 2.0
Formerly known as ABCD ransomware, LockBit has been active since September 2019, but it recently debuted ransomware that the operation has dubbed LockBit 2.0. Recent victims have included consultancy Accenture.
“LockBit 2.0 prides itself on having one of the fastest and most efficient encryption methods in today’s ransomware threat landscape,” security firm Trend Micro said in a recent report.
In an apparent bid to increase the group’s profile and attract new affiliates, a spokesman for the group, who goes by “LockBitSupp,” recently granted an interview to the Russian OSINT YouTube channel, extoling the virtues of his operation program, which he says remits 80% of every ransom paid to the responsible affiliate. LockBitSupp also said operators continues to refine the malware and other tools in an attempt to make attacks not just faster but more automated, including for exfiltrating data and routing it to a dedicated data-leak site.
As of Thursday, the LockBit 2.0 leak site listed 64 victims, some of which had their stolen information already published, and others for which a countdown timer is still running.
6. OnePercent Group
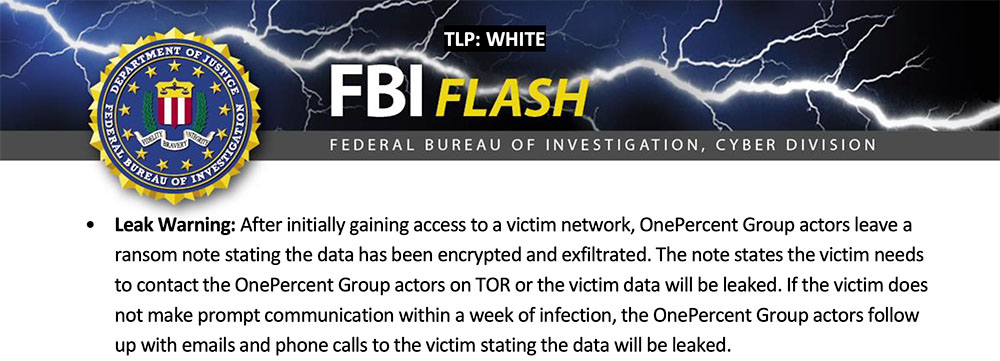
The FBI on Monday released a flash alert on the OnePercent Group, which warns that it has been active since November 2020 and uses phishing attacks to infect victims with the IcedID – aka BokBot – banking Trojan. The phishing emails arrive with zip files containing a Microsoft Word or Excel document that has a malicious macro designed to install the malware, which drops and executes the Cobalt Strike penetration-testing tool.
Together with PowerShell scripting, the attackers move laterally across the network, using the Rclone tool to exfiltrate data to cloud storage before ultimately deploying their crypto-locking malware on every possible, the FBI says.
“The actors have been observed within the victim’s network for approximately one month prior to deployment of the ransomware,” the FBI reports.
After that, “the victim will start to receive phone calls through spoofed phone numbers with ransom demands and are provided a ProtonMail email address for further communication,” the FBI says. “The actors will persistently demand to speak with a victim company’s designated negotiator or otherwise threaten to publish the stolen data.”
For any victims who refuse to pay, the group has previously threatened to sell the stolen data to the REvil, aka Sodinokibi group, it says.
Email security firm Armorblox notes that the indicators of compromise described by the FBI overlap with activity ascribed to the “Shathak” or “TA551” groups, which Mandiant designates UNC2420, as well as an analysis of the IcedID infrastructure detailed in May by security firm Team Cymru.
7. BlackMatter Ransomware
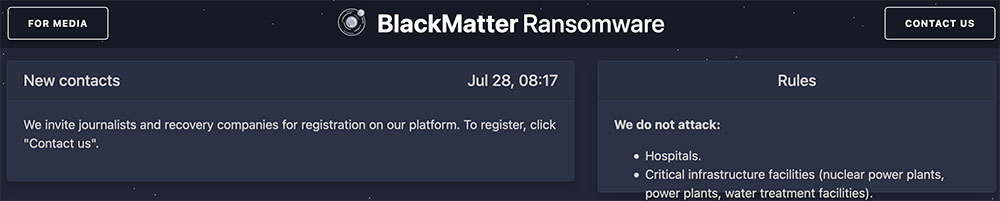
In late July, a cybercrime forum user with the handle “BlackMatter” announced the launch a new operation that “incorporated in itself the best features of DarkSide, REvil and LockBit.”
After analyzing a BlackMatter decryptor found in the wild, however, ransomware-hunting expert Fabian Wosar, CTO of security firm Emsisoft, announced: “I am convinced that we are dealing with a DarkSide rebrand here.” Blockchain analysis firm Chainalysis has analyzed the cryptocurrency wallets being used by BlackMatter, leading it to also conclude that it’s a rebrand of DarkSide.
Thus, predictions that ransomware operators would simply set up shop under a different name appear to have come to pass. “We have known for 50 years that hacking is an addictive behavior,” says information security veteran William Hugh Murray. “It is naive to expect reform. ‘Rebranding’ is much more likely than reform or retirement.”





